Sophos solutions allow for reinforcing Sophos 2FA (two-factor authentication) with Protectimus OTP hardware tokens with one of these two methods:
- Enabling ‘Auto-create OTP tokens for users’ feature. This automatic method allows for using our programmable Slim NFC token instead of the standard application for multi-factor authentication.
- Disabling ‘Auto-create OTP tokens for users’ feature. This manual method allows for adding classic TOTP tokens Protectimus Two or Protectimus Crystal to generate the Sophos one time password.
Both methods have their advantages, but the second one is a bit more lucrative.
Today we will provide you with a guide on how to implement each of the two methods for your Sophos 2 factor authentication and answer the most common questions on Protectimus OTP tokens for Sophos client authentication.
Definitions
Let’s give a couple of definitions for a better understanding of what comes next, so you won’t have to google “What is OTP?” or “what is a token?” First things first — OTP stands for One Time Password. Once generated, one OTP is valid only for one single transaction. Now let’s move to the more complicated matters.
- OTP secret — a completely unique 128bit encryption key, used for password creation. Each user has his or her own secret.
- OTP code — a time-limited one-time code, usually consists of 6 digits and is attached to the user passwords to allow authentication.
- OTP token — an object that assembles each of the necessary authentication elements (User, OTP secret, OTP pass).
| Read also: How does 2-factor authentication work?
How to Enable Automatic Creation of OTP tokens in Sophos
Note: To configure programmable hardware token Protectimus Slim NFC you’ll need an Android smartphone with NFC support.
Virtually every Sophos product comes with this option (Sophos UTM, Sophos Central, Sophos XG Firewall and others).
For example, Sophos Central 2FA can be done via SMS or a 2FA application, which allows for switching to our Slim NFC hardware token. And thus upping the Sophos 2FA security level to the highest. Let’s see the steps to enable this option.
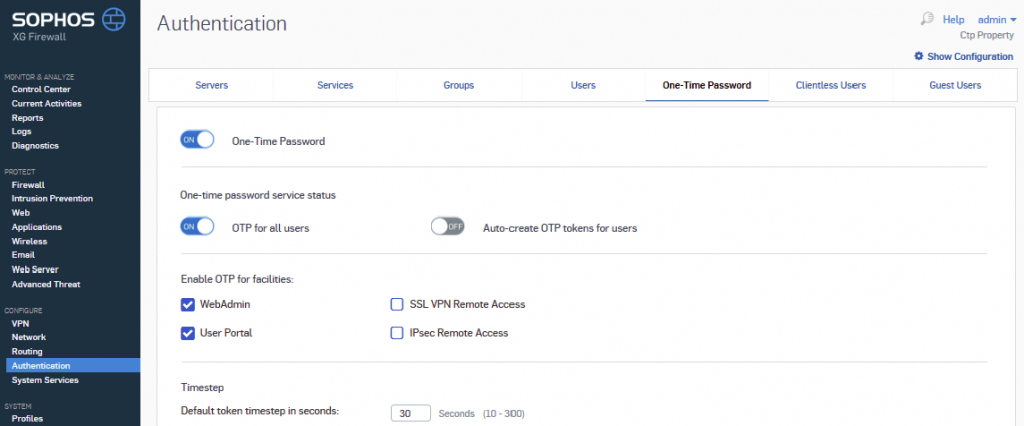
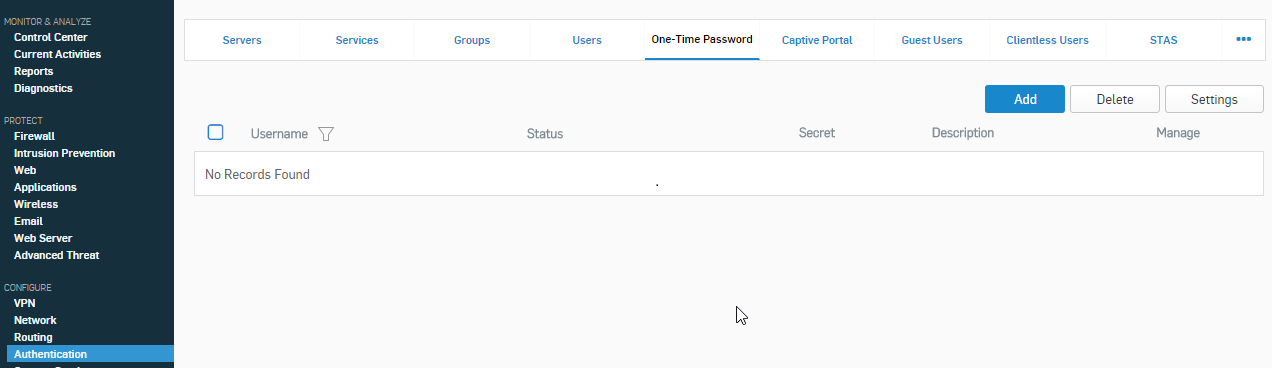
- Go to the One-Time Password tab
To do this go to the Settings section at Configure > Authentication > One-Time Password.

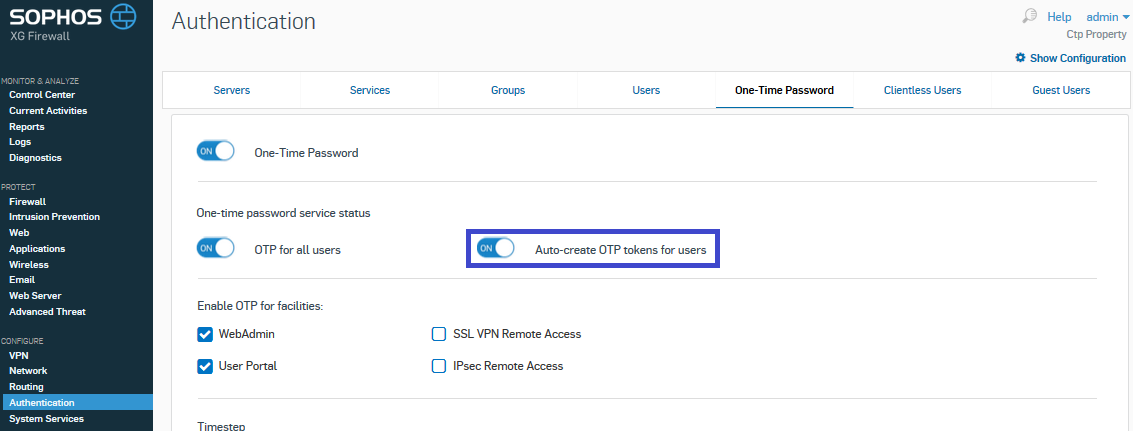
- Enable Auto-create OTP tokens feature
To permit the OTP and Auto-create tokens features, simply switch both buttons to ‘on’, don’t forget the ‘Apply’ button at the bottom.

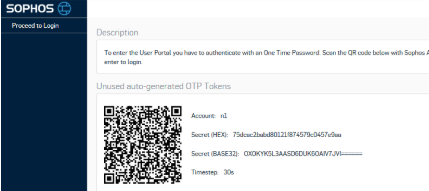
- Get the QR code with the secret key
Go to the user login page at Sophos. Since we’ve turned the auto-create option on, the login page now offers a QR code.

- Configure Slim NFC for Sophos multi-factor authentication
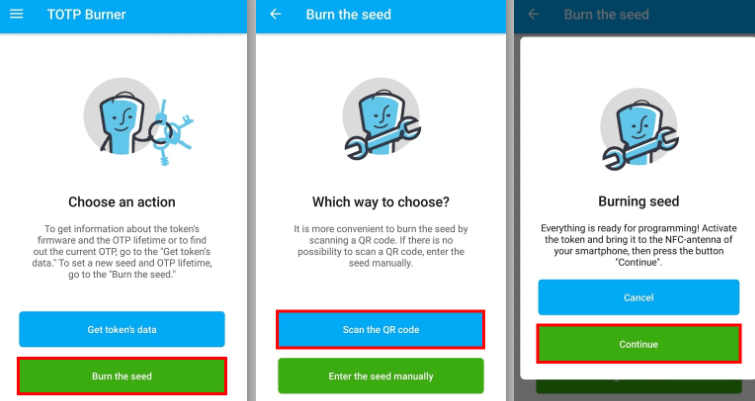
4.1. Download and launch the Protectimus TOTP Burner application (available for Android only).
4.2 Turn on NFC.
4.3. Open the Protectimus TOTP Burner app and click on ‘Burn the seed’.
4.4. Scan that QR code with the secret key using your Burner app.
4.5. As soon as the QR is finished scanning, turn on your Slim NFC token. Hold the hardware device within the range of your phone’s NFC antenna, click “Continue” and wait for the confirmation message. Now your 2FA hardware token is ready to become your Sophos 2FA authenticator.
- Log in by combining your user password with OTP
Return to the User Portal and log in by combining your user password with your Sophos OTP generated using the Protectimus Slim NFC token. The password will look something like this — userpass123456, where “userpass” is the password created by the user and “123456” is the OTP generated by the token.
| Read also: The Pros and Cons of Different Two-Factor Authentication Types and Methods
How to Add Classic Hardware Tokens to Sophos XG and UTM
The following guide is done with Sophos XG user authentication but the steps are pretty much the same for Sophos UTM two-factor authentication. The guides for Sophos UTM vs XG look alike, here’s the one for the unified threat management for you to check out.
1. Enable OTP.
To do this go to the Settings section at the One-Time Password tab in Configure > Authentication, switch the ‘Enable OTP’ feature on.
And set up the necessary timestep depending on the model of the classic hardware token you use:
- 60 seconds for Protectimus Crystal
- 30 seconds for Protectimus Two
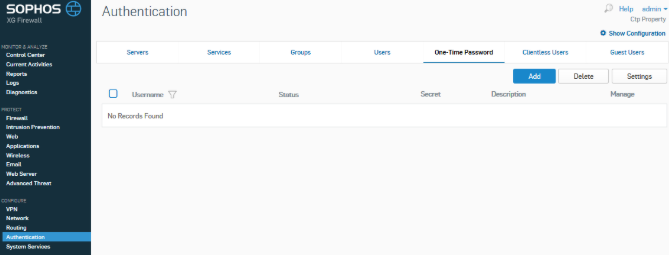
2. Start adding the OTP token manually.
Press the ‘Add’ button to manually add Sophos XG or Sophos UTM OTP token.
3. Select a user and add the secret key
Select a user and add the secret key to authorize this Sophos XG firewall two-factor authentication token to the chosen user account.
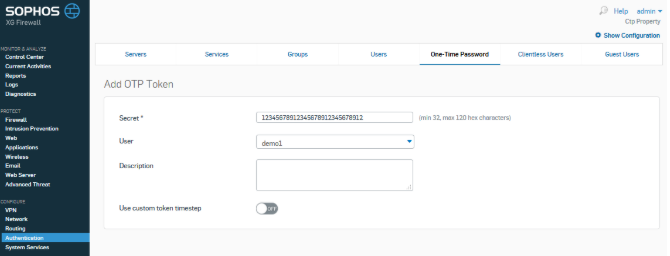
Now the selected account has Sophos XG OTP switched on.
| Read more: 4 Reasons Two-Factor Authentication Isn’t a Panacea
Sophos 2FA Backup Codes
In Sophos XG 2-factor authentication you can have 10 more emergency passcodes in case a user lost the Sophos two-factor authentication device. To create these additional codes go to the user account you want to enable them for and click the edit button. Find the advanced section and the additional codes field at its bottom:
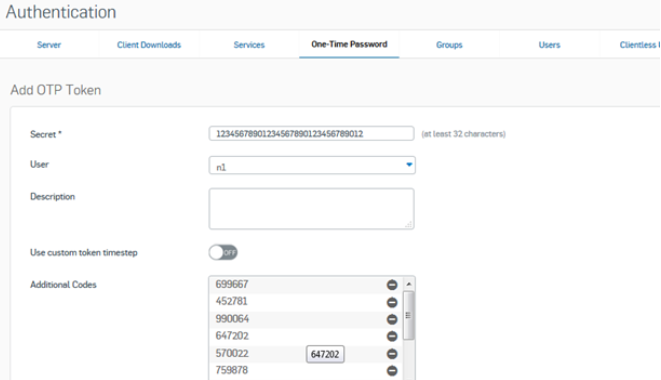
By clicking the ‘+’ you will automatically create 10 additional passcodes each consisting of 6 digits.
The user will have to request an additional code from the administrator.
| Read also: How to Backup Google Authenticator or Transfer It to a New Phone
FAQ
Protectimus Two — $10.99, Protectimus Crystal — $11.99, re-programmable token Protectimus Slim NFC — $29.99 plus shipping.
Any Protectimus order can be as small as only one token.
Sure, the discounts start from 50 pieces an order.
Only one seed at a time is allowed. But the best feature of the Slim NFC token is that it can be reused. You just need to program it for another account once the initial one is no longer in use.
Protectimus Slim NFC device can be branded from as small as one device per order. Protectimus TWO branding can be done from 1000 pieces per order.
Read more:
- 10 Steps to Eliminate Digital Security Risks in Fintech Project
- 2FA Chatbots vs. SMS Authentication
- Time Drift in TOTP Hardware Tokens Explained and Solved
- 2FA Security Flaws You Should Know About
- Office 365 MFA Hardware Token
- Hardware Tokens for Azure MFA
- Two-factor authentication for Windows 7, 8, 10
- PayPal Two-Factor Authentication with Hardware Security Key
- Man In The Middle Attack Prevention And Detection
- Ransomware – to Pay or Not to Pay
Subscribe To Our Newsletter
Join our mailing list to receive the latest news and updates from our team.

Subscribe To Our Newsletter
Join our mailing list to receive the latest news and updates from Protectimus blog.
You have successfully subscribed!