In this article we show how to add a Microsoft Office 365 MFA hardware token Protectimus Slim and Protectimus Flex to your Office 365. You don’t need a premium license to connect these hardware OATH tokens to Office 365 accounts.
With over 31 million users worldwide Microsoft Office 365 is unsurprisingly a bestseller among the productivity software subscription suits on the market. Its compatibility with the major operating systems (both mobile and desktop), the choice of available apps and the familiarity of the brand make Office 365 an obvious choice for a lot of businesses worldwide, from small companies to huge enterprises.
These very reasons and the popularity among businesses make it rather a big target for all kinds of greedy criminals. Being an online platform, with tons of sensitive corporate data stored in the cloud, Office 365 is a low hanging fruit for those hackers. Microsoft understands the vulnerability and supports Multi-Factor Authentication (MFA).
The only bulletproof way of fully protecting your info on a cloud server is Office 365 2 factor authentication with a hardware token. In this article, we will give you the detailed instructions on setting up protection with hardware multi-factor authentication token for Office 365 that can be connected without a premium license.
For this task you will need a programmable hardware TOTP token Protectimus Slim NFC or Protectimus Flex that connects to any website like a 2FA authentication app. So we are also going to address the questions one might have on Protectimus Slim NFC and Protectimus Flex hardware OTP tokens.
Office 365 MFA hardware token: Protectimus Slim or Flex
Azure AD offers a few standard ways to sign in using 2-factor authentication:
- You are offered a mobile app to generate time-based one-time passwords;
- The system can send you a text with a one-time passcode;
- You can choose a phone-call to authorize the sign in;
- And finally, the most bulletproof way – you can have OTP generated by Microsoft Office 365 MFA hardware token, now, Microsoft itself does not provide a hardware device, but third-party tools Protectimus Slim and Protectimus Flex are supported.


A programmable hardware token is essentially a more protected and trustworthy substitution for a mobile 2FA app. Protectimus Slim NFC and Protectimus Flex tokens are the most popular security tokens that work with Office 365. The tools have no Internet connection, so there is absolutely no way your OTP passwords could be intercepted. Protectimus Slim and Protectimus Flex are reprogrammable, this means one device can be reassigned to a different resource over and over again. The programming goes via NFC (Near-field communication) which provides even greater defence.
Protectimus Flex differs from Protectimus Slim Microsoft Office 365 MFA hardware token only in design. Protectimus Flex looks like a key fob, while Protectimus Slim looks like a plastic card of a mini or a banking size card format.
To protect your data with the Protectimus OATH hardware token for Office 365 MFA you need to own an Office 365 subscription with 2-factor authentication on and an NFC Android phone. A premium Azure license is not required.
| Read also: The Pros and Cons of Different Two-Factor Authentication Types and Methods
How to add hardware token to Office 365 MFA
Setting up hardware 2-factor authentication token for Office 365 is easy and straightforward enough, the steps below summarise the process very precisely.
- Download Protectimus TOTP Burner application on an NFC-enabled Android phone.
- Browse to this registration page and sign in with your Microsoft corporate login.
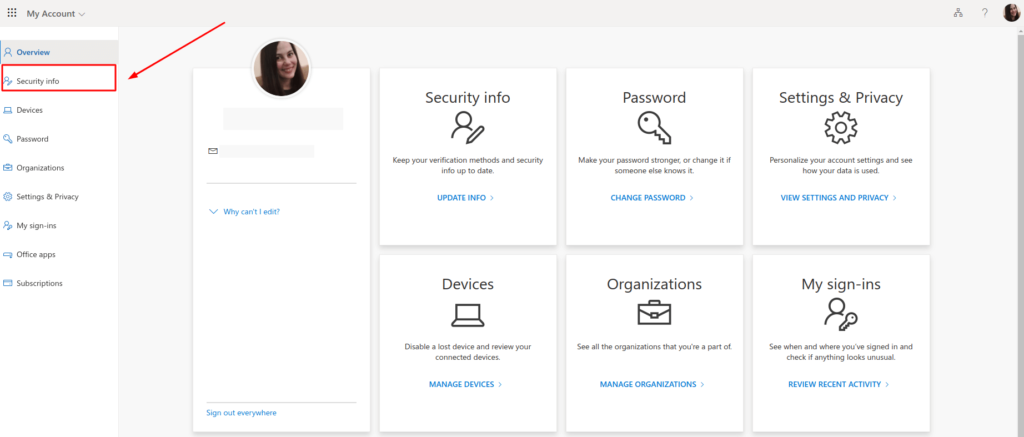
- Go to the Office 365 account settings page at https://myaccount.microsoft.com/?ref=MeControl
- Navigate to the Security Info tab.
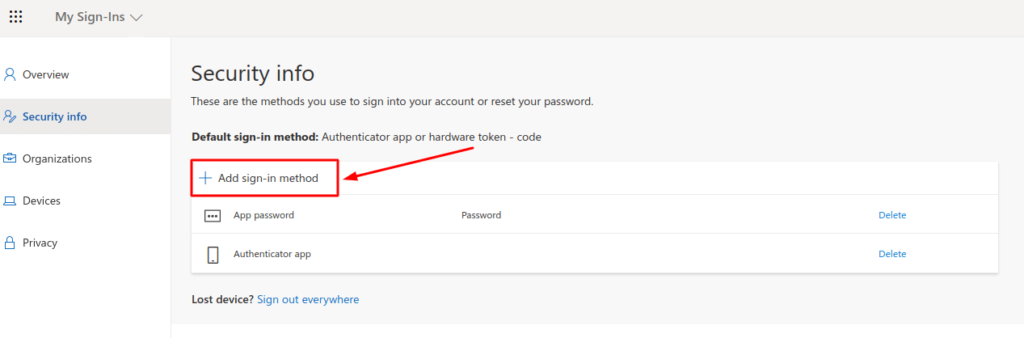
- Click Add sign-in method.
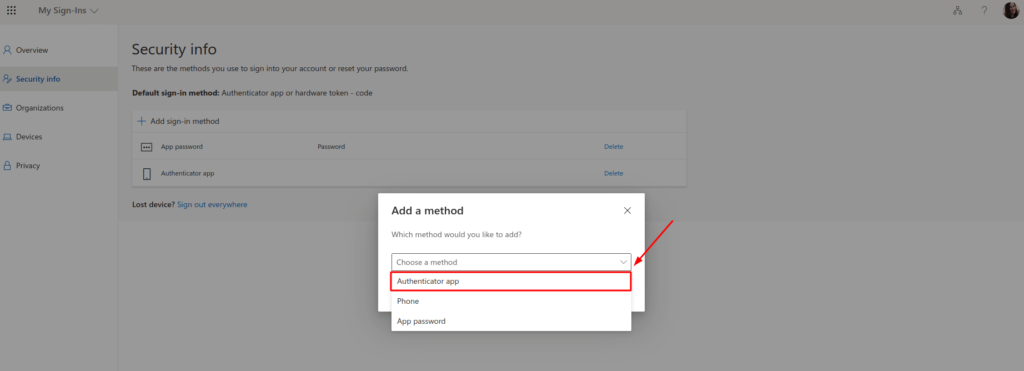
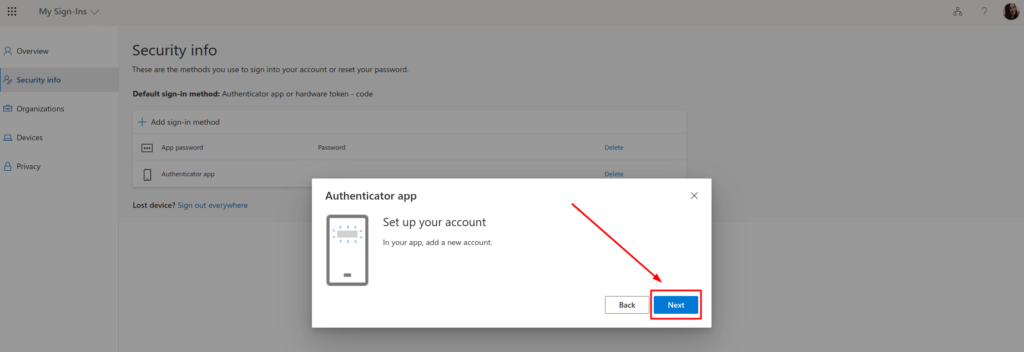
- Select Authenticator app from the drop-down list and click Add.
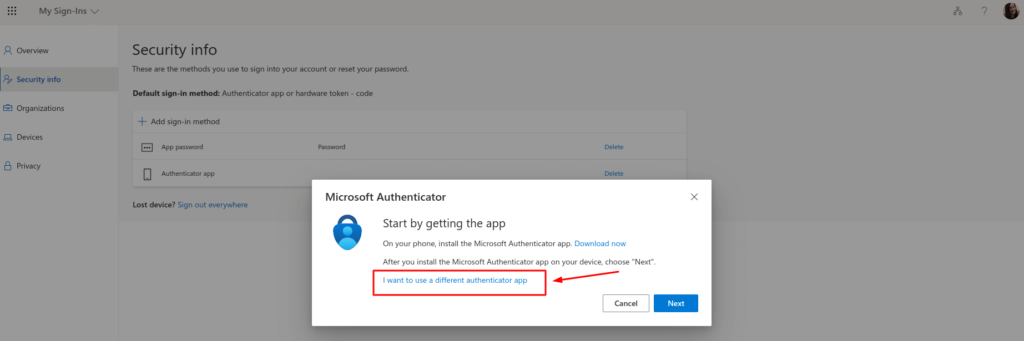
- Click on the line I want to use a different authenticator app.
- Open the Protectimus TOTP Burner application on your phone, make sure the NFC is enabled, and click Next.
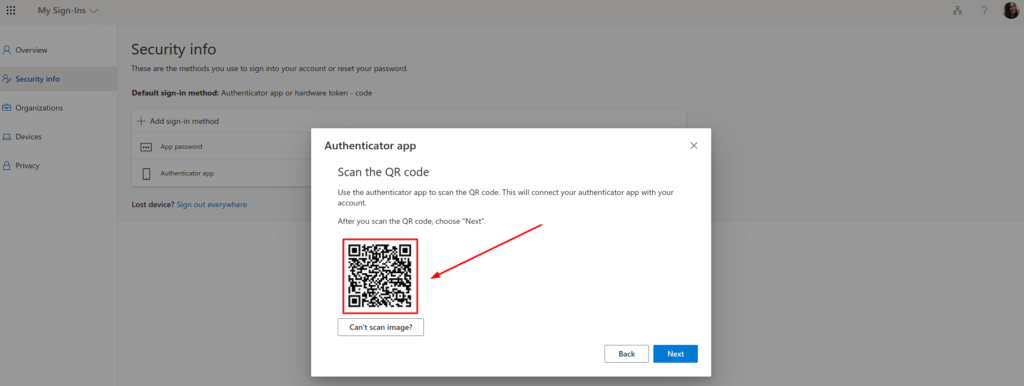
- Now you see the QR code with the secret key. You need to scan this QR code using the Protectimus TOTP Burner app and add it into the hardware token Protectimus Slim or Protectimus Flex via NFC.
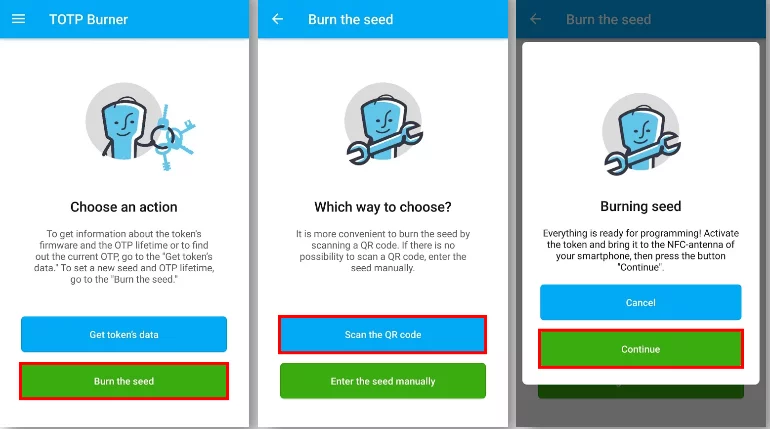
- Launch the Protectimus TOTP Burner app and tap Burn the seed button. Then tap Scan the QR code and scan it. Once the QR is successfully scanned, turn on your hardware token Protectimus Flex or Protectimus Slim and bring it to the phone. Hold the OTP token as close to the phone as possible within the range of your phone’s NFC antenna and click Continue to proceed.
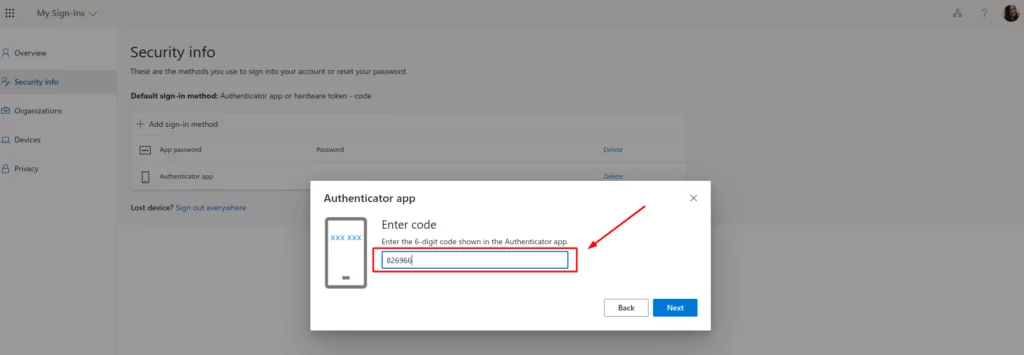
- Once the secret key is successfully programmed into your hardware token for Office 365 all there’s left to do is complete the token registration. Go back to the setup page on your desktop, click Next and enter the OTP code your Office 365 multi-factor authentication token has generated. Then click Next again.
That’s it, now you can log into your Office account the most protected way possible.
Common questions about Office 365 MFA hardware token
Protectimus Slim NFC and Protectimus Flex are truly an impenetrable protection for your data. The mechanism is contactless, the one-time keys are generated by the device itself, there’s no need for a network connection of any kind and the built-in battery allows for years and years of work. These things make it in essence impossible to overtake the passwords, implant the token with any kind of malware code and, as a result, compromise your security, or steal the sensitive information you keep in your Office 365 apps. Besides, if you happen to lose the hardware token you are far more likely to notice its absence before any harm is done, as opposed to an infected app, which can do all kinds of damage without you noticing it before it’s too late.
Absolutely. You can have branded tokens in you order 1000 tokens and more.
Protectimus Slim NFC and Protectimus Flex support only one secret key (seed), so if you have multiple accounts for which you need MFA you will need different tokens. But these tokens are programmable, thus if you stop using an account you can reprogram the token to be used with another account that needs extra protection.
Read more:
- Hardware Tokens for Azure MFA
- Protectimus Customer Stories: 2FA for DXC Technology
- Protectimus Customer Stories: 2FA for Advcash
- Protectimus Customer Stories: 2FA for SICIM
- Hardware or Software Token – Which One to Choose?
- Why US, Canadian, and EU Universities Choose Programmable Hardware OTP Tokens
- How to Program Protectimus Slim NFC Token
Subscribe To Our Newsletter
Join our mailing list to receive the latest news and updates from our team.


2020-06-27
Hey there! Do you use Twitter? I’d like to follow you if that would be okay. I’m definitely enjoying your blog and look forward to new updates.
2020-06-30
Hi Reed, sure, our Twitter is https://twitter.com/Protectimus
2020-08-05
I simply want to tell you that I am beginner to weblog and truly liked your page. Likely I’m going to bookmark your blog post . You really have good posts. Thank you for revealing your website page.
2021-05-25
Hi, I have just purchased the protectimus two and want to use them for MFA for Office365, is this possible and how do I go about it?
2021-07-02
Hi Warren, you need a programmable hardware token to connect it to Office 365. We offer two models of programmable tokens – Protectimus Flex and Protectimus Slim NFC, these tokens will work for Office 365 as you can connect them as if it is a 2FA app. Protectimus Two tokens are not programmable: they are produced with pre-installed secret keys that can’t be changed.