Our regular readers know that we strongly recommend applying two-step verification wherever it’s possible. In the contemporary world, where database leaks are a standing affair, two-step authentication is not an option, it is, in fact, a must. If you use two-factor verification, an intruder would need to get both the unique password you came up with, and the gadget, which produces the verification codes, to break into your account. Thus, two-factor authentication protects from brute force, keyloggers, most cases of phishing and social engineering. It also complicates man-in-the-middle and man-in-the-browser attacks.
So why two-factor verification is still unpopular? Sure, it creates an extra step to take to log in, but most users omit it not because of this extra time and effort, but because they are afraid of losing access to their credentials if something goes wrong with their authentication devices.
“As the world is increasingly interconnected, everyone shares the responsibility of securing cyberspace.”
– Newton Lee, Counterterrorism and Cybersecurity: Total Information Awareness
From all available options of one-time passwords generation or delivery (SMS, emails, hardware and software tokens) most people choose Google Authenticator or other similar applications like Authy, Protectimus Smart etc. Operating principle is pretty much the same for all the software OTP tokens – they generate authentication codes for logging into your account right on your smartphone.
It’s very convenient to use the smartphone for two-factor verification, but there are always these nagging questions: What do you do if you lose the smartphone which generates your one-time passwords? What occurs if you switch smartphones, do you lose the entire account? How do you transfer Google Authenticator to a new phone? In this article, we will answer these nagging questions and help you protect your invaluable personal data.
| Read also: How does 2-factor authentication work?
3 ways to backup Google Authenticator
1. Backup codes
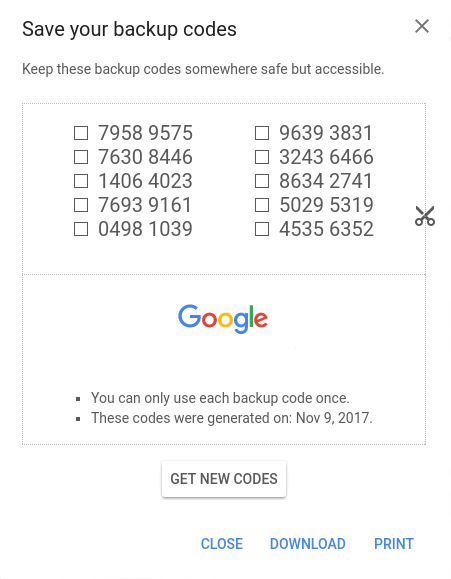
Google, as well as some of the other websites where you can protect your user account with two-step authentication, provides backup codes. These are the one-use codes that allow you to login into your account if you lose access to your OTP token. After you use a backup code once it’s gone for good. Most people print out these Google Authenticator backup codes and keep them at hand.
It is imperative to understand that Google Authenticator is a multi-token, thus you can enroll many tokens for various websites using one app. Some of these websites provide backup codes, and a user can gain access to these websites if his/her smartphone is lost. But what do you do with the websites which do not support backup codes?
Another point against Google Authenticator backup codes is – they are as secure as a password written down on a paper. An intruder can easily copy them if they are in physical vicinity and use them to gain access to your account. Granted, the intruder will have to be among your peers and know the user password, but you know… things happen.
Other things that you might want to keep in mind when it comes to printed out backup codes:
- You do not have them at hand at all times
- You can lose the paper or destroy it by mistake
- Only a few services provide them
Google Authenticator backup codes have their perks, but you have to be ready for the drawbacks as well.
| Read also: Mobile Authentication Pros and Cons
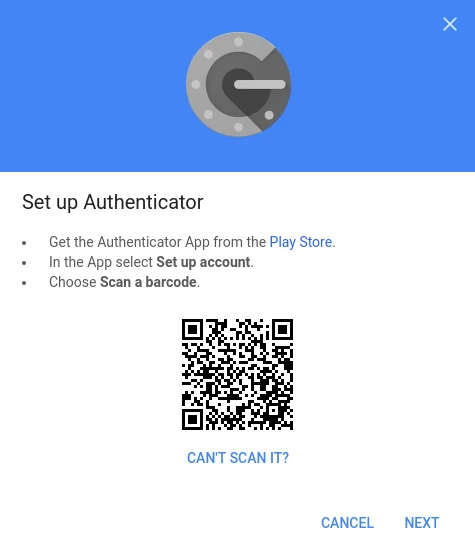
2. Saving screenshots of the secret keys
This is by far the easiest way to never lose access to your account. When you first set up your Google Authenticator simply make a screenshot of the barcode with the secret key. Keep the screenshot very secure though, if someone in your vicinity finds it they can access your data. Please, mind, if it really happens and someone steals your secret key, they will still need to know your user password, so make sure it’s not a simple combination to guess.
3. Programmable hardware token
Created as a more secure alternative to the authentication apps, hardware tokens Protectimus Slim NFC can be used with Google, Facebook, GitHub, Dropbox etc. These tokens are easily programmed with an application for Android with NFC support.
The token looks like a credit card and can be carried with you effortlessly. So you’ll always have an alternative source of one-time passwords on all times, for example, if your smartphone battery is out of charge or you’ve reset the phone or deleted the token accidentally.

The hardware token is far more secure than a backup code on paper or a screenshot of the key – extracting the secret key from the token is absolutely impossible. Protectimus Slim NFC allows for unlimited reprogramming, so every time you change a token on a service you can simply reprogram it and stay protected.
The main drawback here is that one token allows for one secret key only.
| Read also: Hardware or Software Token – Which One to Choose?
How to transfer Google Authenticator to a new phone
Android
1. Use a built-in Google Authenticator feature Transfer Accounts
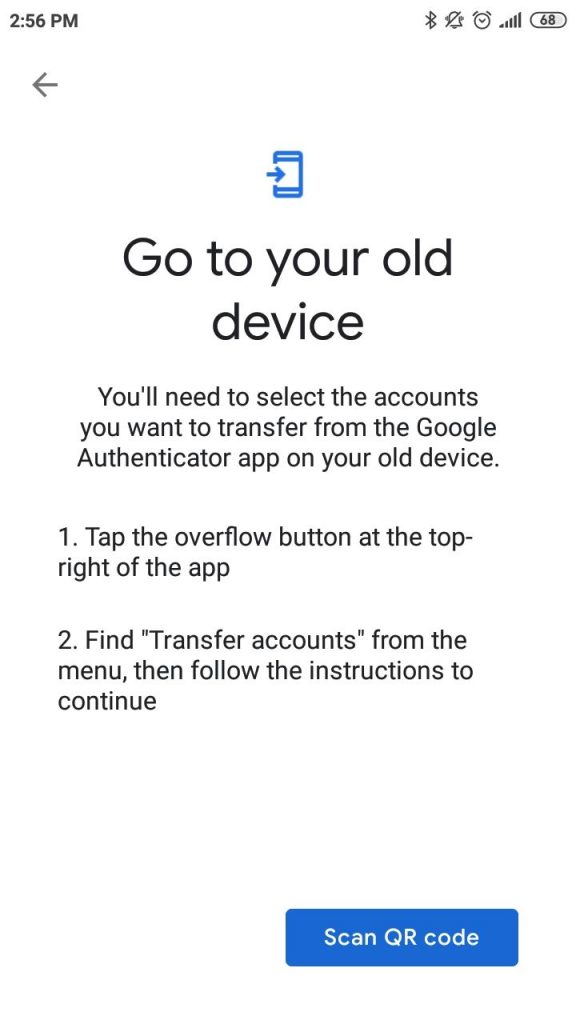
If you use Google Authenticator on Android smartphone, now there is an easier way to transfer it to a new phone. We are talking about a brand new “Transfer accounts” feature added to Google Authenticator recently. Unfortunately, this feature is available only for Android phones so far. If you use an iPhone, please, see the instructions in the next paragraph or here.
There is no need to turn off two-factor authentication on all your accounts and activate it again. It’s enough to tap one button on the Google Authenticator on your old phone, the app will generate a QR code, and then you’ll need to scan this QR code with the Google Authenticator application on your new Android phone. That’s it, all the tokens will be moved.
Here is a step-by-step guide for your convenience:
- Download and install Google Authenticator application on your new smartphone.
- Open Google Authenticator on your old Android phone.
- Tap the menu button at the top-right of the app and choose Transfer accounts.
- Choose Export accounts.
- Select accounts you’d like to transfer to a new phone and tap Next. You have to scan this QR code with the Google Authenticator app on your new phone.
- Now open Google Authenticator on your new Android phone.
- Tap the menu button at the top-right of the app and choose Transfer accounts.
- Choose Import accounts.
- Scan the QR code you have on your old phone. The tokens you’ve selected will be transferred.
Besides, you’ll see a notification “Accounts were recently exported” in your old app. Pay attention to this message. If it wasn’t you, who moved the Google Authenticator tokens to a new phone, take actions. Switch all your tokens in all your accounts to new.
2. Manually Extract Your Credentials [Root Only]
| Note: There are many ways to manually transfer Google Authenticator if you have an Android smartphone with root access to it. We do not recommend using them though. Getting root access can significantly damage the security of your apps and make the device prone to getting viruses and errors. |
This is a more time and effort consuming way to transfer Google Authenticator key to the other smartphone. It requires you to have root access to the smartphones.
To extract the secret keys manually you need to give adb root access, this is easily done with an app like [root] adbd Insecure if you’ve got stock ROM. And in case you happen to have custom ROM you might already have the necessary root access adb, so no additional apps are needed.
Set adb onto insecure mode with the application or directly, connect the smartphone to your PC or laptop and copy the Google Authenticator databases to the computer using the commands.
This is the pathname:
adb pull /data/data/com.google.android.apps.authenticator2/databases/databases
After the file is copied you can open it and see the keys using these sqlite editor commands:
sqlite3 ./databases
select * from accounts;
Now you have your secret keys and can add them to your new device.
| Read also: Twitter Two-Factor Authentication in Details
iPhone
1. Move Authenticator to a different phone using Google account settings
NOTE: You will transfer only the Google token this way. This method works for Android phones as well.
With Google, it is pretty straightforward to transfer the authenticator and all the secret keys within it to another smartphone. All you’ve got to do is go to the two-step verification page, click the “Get started” button, enter your password to verify it’s you, and click the “Change phone” button. Then either scan the QR or barcode, or put in the secret key on the other gadget manually. That’s it.
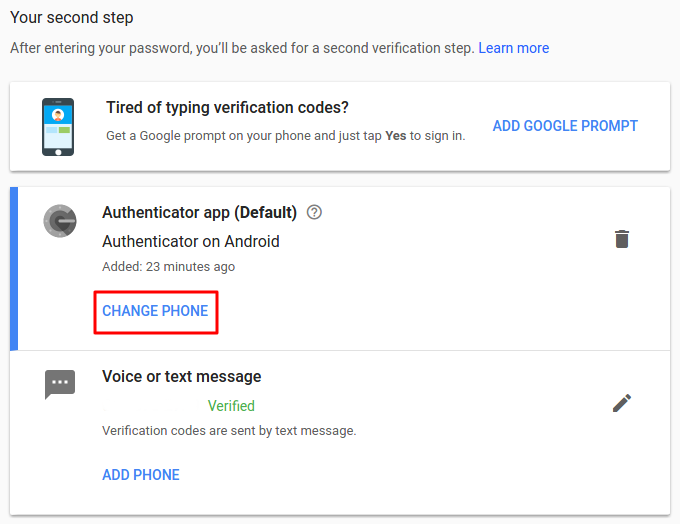
This works only with the Google account, the other accounts where you use Google Authenticator for two-step authentication might not support this option. You will transfer only the Google token this way. So you might want to try the next two options instead.
| Read also: Will Google’s Authentication without Passwords Be Safe?
2. Disable & Re-enable Two-Factor Authentication
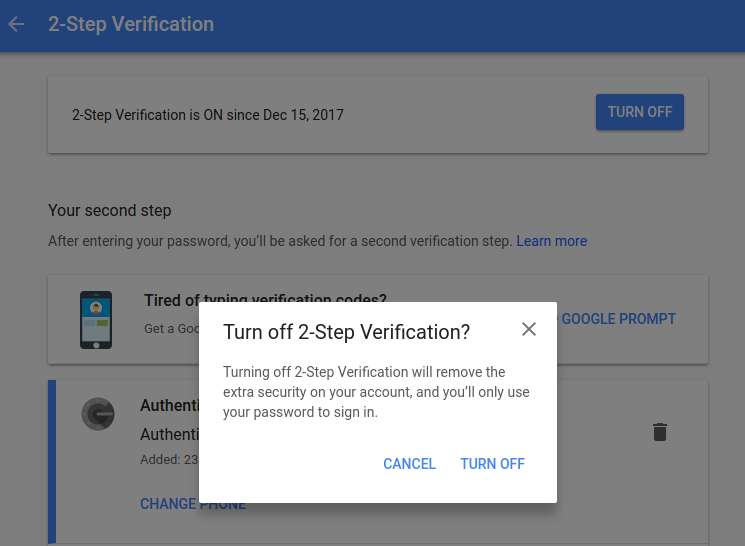
Disabling two-step verification is pretty easy if you still have your old smartphone. It’s usually required to enter the OTP from the currently used token to disable two-factor authentication on any account. To disable 2FA for a while, just click the “Turn Off 2-Step Verification”, “Delete the token”, “Disable 2-step verification” or similar button, depending on the service you use. You’ll find it at the two-step verification page in security settings.
Then add the authenticator application to your new gadget and follow the usual steps to set up Google Authenticator on the new phone.
| Read also: What is Online Skimming and How to Avoid It
Conclusions
Two-phase authentication is a reliable and reasonable way to shield your invaluable personal data. Whether you use a hardware token or apps like Google Authenticator or Protectimus Smart, you now know how to stay safe even if you change devices or lose your smartphone.
We showed you easy ways like Google backup codes and making screenshots of the secret keys. And we showed you more secure option like the Protectimus Slim NFC hardware token.
You also know now how to extract the Google Authenticator data manually, transfer Google Authenticator to another phone and even shut off the two-factor verification if you happen to need to.
So now you do not have any excuses not to protect your info better. All that is left to do is come up with proper user passwords which are not the name of your cat!
Read more
- Remote Work: How to Transition Team to Working From Home During the COVID-19 Pandemic
- 10 Steps to Eliminate Digital Security Risks in Fintech Project
- Credit Card Fraud – Most Common Ways
- Ransomware – to Pay or Not to Pay
- Malvertising: Can It Be Stopped?
- Biometric Authentication Pros and Cons
- Social Engineering Against 2FA: New Tricks
- TOTP Tokens Protectimus Slim NFC: FAQ
- Securing VPN with Two-Factor Authentication
Subscribe To Our Newsletter
Join our mailing list to receive the latest news and updates from our team.


2018-02-06
Hello Maxim,
I have a situation. old phone, (galaxy note 5), has dead screen. Google Auth on it. Of course, lost backup and QR. the program is paired with a crypto currency web site.
Have another Galaxy note 5. Can not log on the the site because 2FA is turned on. Should have stayed with SMS auth. Crypto Site support has been unresponsive. If i load Google Auth. on new note 5, using same SIM(phone number). Will new phone take over Google Auth from old phone? Or is it encrypted based on the EIN? If I an i spoof the new note 5 EIN will it generate authorization to paired crypto web site? Or is there an app that will display a dead screen on PC just by plugging into the mini usb? Worst case,…i will replace the display and problem solved. Just wondered if any other less expensive ways to do it! (Besides saving backup!!) I am stupid. Any help for me? Thanks in advance.
Chris
PS,…Did my Chrome /Google account save the backup somewhere?
2018-02-09
Hi Chris!
Thank you for reaching out. It’s a pity, but Google doesn’t save any Google Authenticator backups. For the future, the easiest backup approach is saving secret keys for every website where you use two-factor authentication. Or, at least, for the most important websites for you. You can save the screenshots with the QR codes, or write down the secret keys, or use Protectimus Slim NFC tokens, which is probably the most reliable option.
I suggest contacting the support team of your cryptocurrency website one more time. If this is not a fraudulent company, they’ll definitely verify your identity, and disable two-factor authentication for you. But if they don’t answer you, unfortunately, there seems to be no other way to restore your Google Auth than to replace the display. It could be possible if your phone was rooted. But now you can’t root the phone as you’ll have to tap several buttons, which is impossible in your situation.
2022-08-03
Hi. I lost my phone so I ended up losing my Google Authenticator and we’ll, and I am not able to login on my Facebook.
I asked a cybersecurity company to Help me with that, and I found out they were scammers.
If I buy these king of generator codes for Google authenticator, will I be able to login on my Facebook?
2018-02-07
I ordered few Protectimus Slim NFC tokens for my sales team last year. It’s the most compact and portable replacement device for the Google Authenticator app I could find on the market. The tokens work flawlessly, the only this is that they are a bit fragile as they are designed to be carried in a wallet or cardholder. But I’ve made a cheap solution from 1mm polystyrene for protecting the Slim to use it as a key fob.
Thing is, phones frequently get lost or stolen. If a salesperson is on the road, and they lose their phone, the first thing they are going to want to do is login to secure their Google account as we are keeping more and more of our assets in google these days. But — catch-22 — they can’t because they don’t have their phone!
The other thing people use is the USB key style devices, but I think they tend to get stuck in laptops and left there. Then the laptop gets stolen on the airport TSA line, and… catch-22 again.
2018-02-12
A little confusing. I already have Google Authenticator installed on my andriod phone and I use it daily. But I CANNOT FIND the original QR code or secret key when I first installed it. I have not lost my phone (yet) but this is very important in case I do lose it or it breaks. I went into my google account and added a 2 step verification and printed out 10 codes which I’ve now placed in a safe place. Please tell me: if I should lose my phone or it breaks, would I download Google Authenticator again? and since I have the 10 codes and can verify my Google account, will it work with my accounts that require Authenticator like before? Will i never have that QR code that I can’t find? thank you, appreciate your help
2018-02-16
Hi Alyce, thank you for the question.
1. You’ll never find the QR code with the secret key you used to create your current token, even don’t try. You can see the secret key (QR code) and save it only once – at the moment when you create the token. Then it disappears, which is right from the security point of view (actually it’s stored on the authentication server and in your phone, but it’s too complicated to pull it out and you actually don’t need this).
2. It’s very good that you’ve saved 10 Google backup codes. Now if something happens to your smartphone you will easily disable 2-step authentication and restore access to your Google account. But please note, if you use Google Authenticator app for any other website (Dropbox, Facebook, any payment system ect.), Google backup codes won’t help you to restore access to any account except Google.
3. What can you do to backup the secret keys for all other websites where you use two-factor authentication? You can log into every account using current tokens, disable or delete two-factor authentication, and then enable 2-factor authentication one more time and create new tokens, saving the secret keys this time.
2018-04-26
Hello, you should definitelly edit the article and clarify this. I was also consufed not to find any backup option in my Authenticator app. Just say that backup is ONLY possible when initially adding a new account into Authenticator and that’s it. Thanks
2018-04-26
for example you don’t mention at all what are these Backup codes and how and where to display them…
2018-02-13
It seems the Google Authenticator backup codes and screenshots of the secret key have the same vulnerabilities – They are only as safe as the paper its written on. So I ordered one Protectimus Slim NFC to test it with my Google account. The token works very well and is ideal for my needs. I’ll be ordering more for my colleagues in due course.
2018-02-14
Hello. I’m really hoping you can help me. I invest in cryptocurrency and use the Google Aunthenticator for the 2-step verification. Last week I upgraded to a new iphone, but with the same number. After connecting my iphone to my computer and restoring the backup, the Google Authenticator was not working. I downloaded it again and it keeps asking me for the barcode or enter manually. I don’t recall it giving me a “key” to use later. I searched my emails for a screen shot of it, but nothing. Now I can’t get access to barcode on any of my crypto wallets because I’m already a client per se; meaning all I need is my login information and the 2-step verification…which I can’t get. What can be done and why when I restored my phone does the google authenticator no longer work? Please advise if you’re able to assist. Kind Regards, James
2018-02-16
Hello James!
Unfortunately, this is a common issue for many iPhone users, Google Authenticator can’t be restored from iCloud backup. If you don’t have access to your old iPhone the only thing you can do is to contact customer support for every cryptocurrency exchange you use. There should be a way to restore access to every legal website. Maybe you’ll be asked to provide some documents for verification, it’s a normal practice for many payment services.
2018-02-15
Thank you, author, you saved a lot of my time and nerves with this article.
2018-01-30
Dear Dirk!
I am really happy to give you a piece of my knowledge.
I’ll continue to work for you 🙂
2018-02-22
Another option for backups is Authy (you briefly mentioned it, but not in depth). Yes, it stores your secrets “in the cloud”. Yes, part of the authentication method that it uses is SMS (which is technically against best standards for 2FA). What it excels at is the ability to back it up automatically. You can set your own encryption key as well. The methods that you mentioned are good if you always follow best practices for security; but the average user will never do so. (Heck – I’m a infosec engineer, and even I have a hard time following all best practices 100% of the time.) That’s where it comes down to a risk assessment. The chances of your secrets being lost through Google Authenticator is astronomical compared to the chances of a breach in a service like Authy. Not all sites support hardware authentication (I love my Yubikey; but very few services that I use 2fa on support it).
There’s another part to the equation too… if someone gains physical access to my device, then my secrets in GA are compromised. There’s a good chance that one or two of my passwords are in memory; so I have to assume those are compromised as well. Yes, my phone is encrypted… but the problem with phones is that people (myself included) leave them on all the time – which means it will most likely be in a decrypted state when it is obtained by another party. With Authy, I can set it to require my encryption key whenever I open the app – meaning the secrets are much less likely to be compromised unless the attacker can brute force or guess my encryption key. From that respect, Authy has some security advantages over GA.
In the end, the biggest problem facing 2fa is that people think it’s too complicated. These methods for backing up secrets are great… if you’re willing to put the work into it. Most people aren’t, so they just will not do it if this is their only option. The best security mechanism is the one that people use – which means it needs to be easy to use. That’s where Authy makes more sense than GA. Both are great options, and it really doesn’t matter which one you use, as long as you use one. 🙂
2018-02-22
I should clarify… when I say “The chances of your secrets being lost through Google Authenticator is astronomical compared to”…, I should have phrased it as “The chances of your secrets being lost through Google Authenticator is astronomically higher compared to”…
Sorry for the confusion.
2018-09-26
Thank you very much for the feedback. You are quite right, it’s better and more convenient to use a 2FA app with backup. Though not only Authy has a backup function. For example, Authenticator Plus offers backup in its paid version, and we are working on adding a backup feature to our own Protectimus Smart OTP app, the release coming soon. Recently we compared 10 most popular 2-factor authentication apps and tried to figure out which one is the best. Take a look, maybe you’ll change your mind about Authy, or vice versa, make sure that it’s an excellent application https://www.protectimus.com/blog/10-most-popular-2fa-apps-on-google-play/
You also wrote that not all sites support hardware authentication and very few services that you use 2FA on support Yubikey. We suggest using Protectimus Slim NFC with all these websites. If the website supports in-app tokens, most probably it supports Protectimus Slim NFC too. Just check the secret key length, Protectimus Slim NFC supports secret keys up to 32 symbols in Base32. And note, you’ll need an NFC enabled Android smartphone to program the token.
2018-03-19
how do I set it up for my Hotmail account
2018-09-26
Hi Ron, we’ll publish a 2-factor authentication set up guid for Hotmail soon. I’ll keep you updated.
2018-08-14
this article is MISS LEADING because you explained that there is no way to recover when you lost phone, maybe only on Google account. So it’s risky if you don’t know this prevention steps
2018-09-26
Dear Roman, thank you for the feedback. When I wrote this article, I meant that people would read it before they lose their phones. It is impossible to backup something you’ve already lost.
2018-09-12
Hi Maxim,
I am trying to transfer my Google Authenticator app from my iPhone 6S to my new iPhone 8. Fortunately I can still access the authenticator from my old phone but I am having difficulty in transferring to my new phone. When I click the link in ‘Step 1’ from your guide above, I am not being given the option to ‘Change phone.’ Instead the only option I have is ‘Set-up.’ I am afraid that if I proceed with setting up on my new phone, that I will lose my accounts that I can currently access on my old phone. Do you have any advice?
2018-09-26
Hi Cian! First of all, I should admit that Step 1 of this article allows you to transfer ONLY the secret key for Google account, the other accounts where you use Google Authenticator won’t be moved to your new phone. But you can disable and re-enable two-factor authentication on other accounts as far as you have the old phone at hand.
I don’t know exactly why do you see the ‘Set-Up’ button instead of the ‘Change phone’ button. The only thing I can suggest in this situation is to download the backup codes and use them if something goes wrong.
2019-01-02
I think this poster (Cian) is not using Google Authenticator for MFA on their *Google* account. I had this same confusion, I assumed that my Google account ‘controlled’ by entire Google Authenticator app.
2019-04-03
I couldn’t agree with you more. This is a common misconception.
2018-09-12
Hi there,
I am having difficulty transferring Google Authenticator from my iPhone 6S to my new iPhone 8. When I follow Step 1 of your guide above, the Google webpage does not give me the option to ‘Change phone.’ The only option I have is ‘Set-Up.’ This generates a barcode, but my fear is that if I proceed, I will lose the accounts that I have on my older phone. Do you know if this will be the case or if my accounts will then transfer over to my new phone?
2018-09-15
My I Phone had google authenticator on it for all my accounts and now after my phone has updated the authenticator has no record of any of the 2FA’s I set up. It is like opening a new authenticator. What has went wrong and can I recover them? Please advise
2018-09-26
Unfortunately, there is no way to restore all the tokens you had. You’ll have to contact the support services of all the websites, where you used two-factor authentication. Or use the backup codes for websites, which offer this option. If you downloaded the backup codes beforehand, of course.
2018-10-20
I have to thank you very much Maxim you have given me some valuable info on how I can store my backup as I am using google authenticator and by screenshots, I have a big chance to rest if it happens that I lost my phone. Thank you once again.
2019-04-03
Thank you for the awesome feedback. I’m glad that this article has proved to be useful to you.
2018-10-24
I have backup codes from google apps. but when I tried to restore the code all of them are invalid ?? please Help !!
2019-04-03
Thank you for the comment. Unfortunately, I do not know how to help you in this situation and can’t assume the cause of the trouble you faced. The only thing I’d like to emphasize is that the Google backup codes are only good for the Google site itself. They don’t help to restore access to any other website except Google.
2018-11-09
I just restored backup of my iphone 4 to my iphone 4s and my google authenticator is not showing any code. I am really in trouble because I don’t remember on which website I used google authenticator.
Can anyone guide me how can I extract codes of website from back up of iphone4, it is dead and I have only 1 month old backup.
2019-04-03
It’s sad, but it seems like in this situation you’ll have to reach the support services of all websites where you used Google Authenticator. Sooner or later you’ll definitely find out where you used the GA app as you won’t be able to access your accounts on these websites.
2018-12-16
I just update to a new phone- iPhone 6s to an Xr, I (had) been using Google Authenticator for all my WOrk related cloud accounts where we have mandatory MFA enabled. On my personal accounts, I had set up and used Authy for quite some time.
This is the first time I have changed out a phone since I have been actively working on the cloud. The Authy transfer to a new phone was pretty straightforward and easy and I retained access to all my accounts. Not so good with Google Authenticator.
The process to transfer to a new phone is SERIOUSLY flawed and not thought out by Google at all. You can create a set of backup tokens but those are only good for the Google site itself. So unless you screenshot the QR codes of all the sites you use GA with your pretty much just F%%Ckd by Google on this and now have to delete your old MFA and sign back up again to access your accounts.
So it’s Sionara Google Authenticator. From now on I will instruct all users to set up an Authy account. Its more of a process than GA is to set up, but way more secure and the process for back-ups etc WAS thought out with customers in mind. Google just doesn’t give a rat’s A$%$ from what I can tell.
2019-04-03
Thank you for the comment, Tom. You are right, Google Authenticator doesn’t provide the backup feature out of the box. That’s why I decided to write this article and inform readers on what to do to avoid an unpleasant situation you described above.
And of course, there are much better 2FA apps with backup features on the market – Authy, Authenticator Plus, Protectimus Smart are among them. We described the best 2-factor authentication apps in the article “10 Most Popular Two-Factor Authentication Apps Compared” – https://www.protectimus.com/blog/10-most-popular-2fa-apps-on-google-play/
2019-01-02
Is the original QR code the permanent TOTP token, i.e., making a backup of it (during setup of each account) allows you to recreate all the accounts on a new phone?
I had always understood the QR code to be a literal one-time token which generated the permanent ‘seed’, i.e., that QR code could not be re-used to regenerate the original seed.
______
I have read that iPhone users have successfully restored their entire Google Authenticator configuration through their iCloud backup, i.e., iCloud was synching the complete dataset. Is this possible through any Android backup utilities? I am assuming the default Google backup does not work. But what about Samsung’s or any other third-party option? Maybe you need to use something like Titanium Backup with root-access?
2019-04-03
Yes, the QR code is the permanent secret key (seed), used to generate one-time passwords according to the TOTP algorithm. The app scans the QR code and saves this secret key. Then the app will use the secret key and the current time interval to generate one-time passwords. If you save the secret key, you’ll create exactly the same token next time. That’s why it is so important to store the saved QR codes in a reliable place.
______
As far as I know, security policies don’t allow saving such sensitive information as secret keys, on Android for sure. That’s why there are so many troubles with 2FA apps’ backup. With root access, you’ll probably backup any info and secret keys as well, so Titanium Backup with root-access sounds like a good idea.
2019-03-12
terribly written article does nothing to describe the specific process to backup each 2fa account. HOW DO YOU DO IT? If you’re going to write an article called google authenticator backup you need to explain how to backup.
2019-04-03
Thank you for the feedback, Shawn. I’m very sorry that this article disappointed you.
As far as I know, there is no other way to backup the tokens from Google Authenticator than saving the secret keys you used during these tokens’ enrollment. There are too many websites in the world that use 2-factor authentication and allow using Google Authenticator. Thus, it requires enormous efforts and time to describe the specific process to backup each 2FA account. Maybe we’ll launch a similar project in the future.
2019-03-27
hey Maxim,
how do I submit a second secret key with google authenticator?
like I did the first no problem but now it is asking me to scan a QR code which I do not have.
Any help will be appreciated.
thanks,
Kevin
2019-04-03
Hi Kevin, if you don’t have a QR code, maybe you have a secret key in another representation – a string of letters and numbers (something like this – 4QCT HPE7 VI5U C5BH HWHK N3VQ YHAE 6TBU)? If you have a secret key in this form, you can add it to Google Authenticator manually.
When you tap the red button “+” in the lower right corner, you see 2 options – “Scan the barcode” and “Enter a provided key”. Just choose “Enter a provided key”, enter any Account name you wish, and enter your secret key. Then tap the button “ADD”.
Please, let me know if this advice is useful for you. If not, provide more details of the issue you face, and I’ll try to advise a better approach.
2019-04-09
Hi Maxim. Thanks for the article. The pulling out keys through adb was what I was looking for! But it didn’t work for me initially, as pulling just the databases file wasn’t enough. I checked the file storage through recovery (I was not able to boot, and that’s why needed the keys in the first place), and there were three files: databases, databases-wal, and databases-shm; I had to copy all three of them to read the database. I am not sure if this is a recent thing, but maybe you can update the article with this information.
2019-06-05
I think the best way to back up Google Authenticator is to save the the actual keys (text strings). I keep the GA keys for my 2fa accounts in an encrypted file in the cloud.
Today I went to enable Google Authenticator on a financial site and guess what — they don’t provide the “enter key” option. It showed only the QR code.
To get the key, I opened my QR reading app and scanned the G-Auth QR code. The app showed the text string and I copied it down.
2019-10-06
Great! Thanks a lot foг the guide!
2020-02-27
What happens if you physically lose the credit card token protectimus? Can you just order a new one, or is your account gone?
Thanks
2020-03-17
Hi Rick! The secret key is stored on the card only. Neither the application Protectimus TOTP Burner, which is used to program the token, nor our company store the secret key, so we can’t help you to restore access to the website even if you order a new token. It’s the same story with Google Authenticator. To avoid such situations, you better save the backup codes, or enroll two tokens with the same secret key (a hardware token, and a software token), or store the screenshot of the secret key in a very safe place.
2020-06-16
Everything is very open with a really clear explanation of the issues.
It was really informative. Your site is very useful.
Thanks for sharing!
2020-09-29
I transferred one of my Google Authenticator accounts from my old phone to my new phone. Now there is a blue message “Accounts were recently exported” on my old phone. And another message “Accounts were recently imported” on my new phone, when I open Google Authenticator. How do I clear or remove these messages? Thanks.
2020-10-12
I wonder if Goole Authenticator can backup all our accounts in the cloud space like LastPass authenticator to recover and import them after a reset factory of a phone or not? I ask this question and it’s important to me because a few months ago, had to reset factory my cell, after then I found out I can’t log in to my Facebook account and needs 2FA code, and all my accounts in Google Authenticator lost and now I can’t log in to my Facebook account!
While LastPass authenticator has the ability to backup all accounts to its cloud space and recovers them again after a crash for cell or a reset factory experience like I had without worrying.
I didn’t any option to backup all accounts in the cloud in GA or maybe it has and I can’t find it.
2020-10-12
Dear Masoud, Google Authenticator doesn’t back up all the tokens in the cloud. If you factory reset the phone before you transfer the tokens to another phone, you’ll lose all the tokens and, consequently, access to all the accounts you protect with 2-factor authentication. To avoid this, you can back up your tokens by saving screenshots of the secret keys or using programmable hardware tokens Protectimus Slim NFC. Or choose another in-app authenticator with a cloud backup feature.
2021-08-04
What I’ve noticed when I tried to Export my GA tokens on an Android phone is that the app created a QR code with all selected tokens that I have to SCAN with my New phones’ GA app.
What if I just save THAT QR code as a backup?
What if I take a photo of it and store it somewhere safe?
Not Import it in a New GA app on a New Android phone imediately, but in a few months or years?
Can this be done in such a way?
Thanks in advance…
2021-12-07
This isn’t helpful if you want to factory reset your phone.
Why can’t I just export a file, and import that file later?
I tried taking a screenshot of the QR code but it’s just blank.
2022-01-10
Finally I’ve found something which helped me. Many thanks!
2022-01-18
Hello. And Bye.
2022-03-12
I appreciate, cause I found just what I was looking for. You’ve ended my 4 day long hunt! God Bless you man. Have a great day. Bye
2022-03-15
Everything is very open with a clear description of the issues. It was definitely informative. Your site is useful. Thank you for sharing!
2022-04-26
Thanks for sharing. I was confused about that the backup code can only show up once on my authenticator.
2022-06-27
It ís difficult to find educated people in this particular subject, but you seem like you know what you’re talking about! Thanks