I guess that’s not only me, who’s tired of passwords: we should remember them, they should be strong enough not to be guessed or brute forced, and even more, they should be different for each website. But it has recently turned out, that not only I think so.
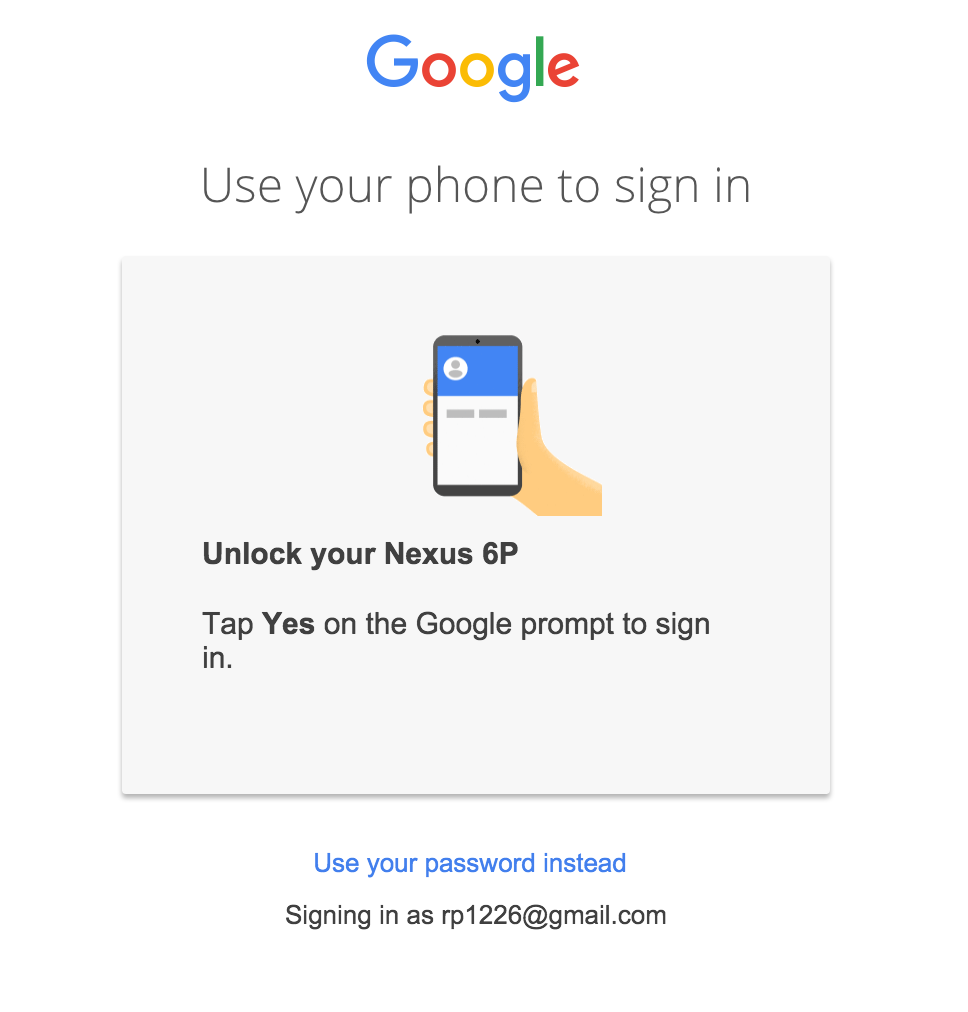
A few days ago I have come across the information that Google is testing a new system of authentication without passwords that will allow refusing the password entry when logging into the account. User authentication will be reduced to simply clicking ‘Yes’ button on a smartphone, thus confirming the identity and getting access to the account.
Being a specialist in information security, I decided to share my opinion about this authentication solution. There are some doubts about its feasibility and security. Besides, I would like to find out what do you think about it.
The data exchange is performed via GCM (Google Cloud Messaging). When the notification is sent to the user’s device, he or she should accept it to log into the account.
According to the Rohit Paul, who have informed the world about this innovation, the system works according to the two-factor authentication principle. At first, the user needs to log into the smartphone (the first factor), and only then he will be able to accept the Goggle’s notification and enter the account (the second factor).
But I dare to disagree as this scheme has a few ‘buts’:
- It would be a serious mistake to consider this method to be a real two-factor authentication. When clicking the button ‘Yes’, the user actually confirms only one factor – the factor of owning the phone. The second factor (knowledge) is not checked by the system. 2-factor authentication involves the use of two different factors at the same time – a knowledge factor + ownership factor or biometrics. The key idea of 2FA is that the advantages of one factor can overlap the downsides of another one.
- If your smartphone is locked, lost, or you simply cannot reach it, you can enter the account with the usual login and password. This means that the second factor is optional. What will prevent an attacker from taking advantage of this loophole? It is not a big problem for a hacker to get the password using phishing, social engineering, brute force, etc.
- In fact, such an innovation can even make the situation with the account protection worse. The attacker now will even have a choice – either to guess or steal the password or to infect the user’s smartphone with a virus. It is worth mentioning that 87% of Android smartphones are vulnerable. The bulletins about the iOS vulnerabilities also creep in from time to time.
The new authentication without passwords system with signal transmission via GCM, which is being tested by Google, is obviously not designed to strengthen the data protection. Perhaps, such a scheme is suitable to simplify the login process as the user needs only to press a single button. In this case, I agree, it is convenient and pleasant for most users because all people are lazy by their nature.
But if taking the data protection seriously, in my opinion, it is better to stay off the authentication without passwords method and use 2FA with one-time passwords instead. Today, there are many free applications for one-time passwords generation – Google Authenticator, Protectimus Smart, etc.
Subscribe To Our Newsletter
Join our mailing list to receive the latest news and updates from our team.


2016-01-12
It is too early to judge the product or feature when it is only at the development stage. Your arguments are quite logical, but Google didn’t lay its cards on the table yet. I’m sure at the release stage we’ll see a worthy and safe solution. I like the idea of convenient authentication.
2016-01-12
Of course, anything is possible. I hope that Google will surprise us and create something revolutionary. The idea is good when viewed from the standpoint of convenience. I just wanted to say that it is not quite right to call such authentication two-factor because in its essence it remains one-factor. The system checks the smartphone ownership factor or the factor of knowing the password (if the phone is not at hand), but not both of them at the same time.
2016-05-12
Thank you for that good post. I really like it.
2017-07-13
May I just say what a relief to uncover somebody who truly understands what they’re discussing on the net. You actually understand how to bring an issue to light and make it important. More people should check this out and understand this side of the story. I was surprised that you aren’t more popular given that you definitely have the gift.
2023-07-04
wonderful post, very informative.