What do advanced network hackers have in common with run-of-the-mill scammers lying in wait for unsuspecting victims on the street? Both of them make extensive use of social engineering. …though many of them don’t even know this term.
Social engineering refers to a method of acquiring desired information by using psychology; in particular, the weakness of the human factor. The fact that the reaction of Homo sapiens is largely predictable. Knowing this, it’s possible to “program” the behavior of both individuals and groups.
Examples of social engineering can be found both online and in everyday life. It’s used in marketing and political campaigns, for which terabytes of information about people’s preferences and habits is gathered in advance. After all, knowing typical behavioral and preferential patterns makes it possible to target advertisements that encourage people to buy something, order something, or vote for a particular candidate. Practices like these certainly aren’t going to please everyone, but at least as far as legal collection of information is concerned, citizens do have the option to not share their data. For example, internet users can prohibit sites from tracking their search and geolocation history.
The criminal application of social engineering techniques is first and foremost to obtain some desired confidential information, naturally without any thought as to the victims’ wishes.
The standard procedure used by these social hackers consists of several basic steps:
- Choosing a valuable target.
- Collecting data on the target in order to find the most vulnerable avenue of attack.
- Creating a scenario based on the collected data — this scenario should coerce the victim into taking some action desired by the attacker. (On the internet, the goal is usually to facilitate unauthorized access to a computer system, bypassing authentication and other security measures.) Speaking of coercion: it’s important to note that there is no outright force involved; instead, the manipulation is transparent to the target, who thinks they are acting of their own free will.
We can model such a situation, in which the victims themselves turn to the attacker for “help”. For example, a flyer with the contact information for a tech support service is left in some conspicuous location in an office, and the attacker remotely creates some sort of problem on an office computer. As a result, the user him/herself turns to the attacker, and in the process of “solving the problem”, they disclose the information desired by the attacker.
Basic social engineering techniques
Phishing
One way to obtain confidential information from the user is through phishing. In this technique, an e-mail is sent to the victims, supposedly from their bank or some other authoritative organization, asking the user to enter some information into a form, such as a username, password, card number, or PIN code. In addition to revealing sensitive information to the attacker, the phishing victims also risk having their devices infected by malware when navigating to the fake website or filling out the form. (We cover the dangers of phishing and how to protect yourself from it in another post.)
Trojan Viruses
Trojan viruses are a variation on the previous method, typically also distributed through e-mail. Instead of a fake form to fill out, the email features an attachment containing malware which can collect or modify data on the user’s computer at a later time.
Pretexting
Rather than e-mails, this technique usually uses voice-based methods of communication: telephone calls and various messaging applications. In order to apply the technique, some information on the “target” must be gathered beforehand in order to earn the target’s trust (e.g. name, title, projects an employee works on, names of colleagues and superiors). Pretexting makes use of preconceived conversation scenarios designed to coerce the target into revealing information or taking a certain action. For example, an attacker can call a company’s IT help desk with a request to recover the password to “his” account.
Unfortunately, “social hackers” have no shortage of information about future targets. For scammers, social networks represent a veritable fountain of information on millions of people. That information is all provided voluntarily, often with pride, even: pictures of the new house and iPhone, place of work, detailed reports on travel, names of friends, colleagues, children, loved ones. You wouldn’t dream of handing this information over to the first person you see on the street; and yet, it’s all available freely online.
Pharming
This technique makes use of hidden redirects to fake sites. With the help of malicious software, the user is redirected to a fake copy of the web site they intended to visit. This technique is particularly dangerous because it’s usually very difficult, if not impossible, to discover. After all, the user themselves inputs the correct address into the browser! Where they end up after that, well … that’s of no concern.
Why these methods work
The essence of social engineering lies in how the attacks bypass critical, analytical thought, focusing first and foremost on emotion. And many people who are engaged in mentally demanding activities (including the majority of office workers) tend to suppress emotional outbursts. This is what makes social engineering so effective. The attacker’s intelligence, thus, may even be significantly lower than that of their victims. But social engineering methods rely on emotion, not intelligence. This also explains the success in cultivating “suckers” enjoyed by professional criminals, who typically are possessed of rather low mental capacities. In order to prevent their unwitting subject’s mind from “interfering” in the process, attackers often attempt to block it out, overloading it with insignificant background information. In practice, the attacker may accomplish this with incessant chatter, talking the victim’s head off, so to speak.
The attacker’s trump cards are suddenness and an artificially-created sense of urgency (or, better yet, urgency and fear). In a situation where a decision must be made immediately, there is no time to verify the information provided by the attacker, so a decision is reached based not on thoughts, but on feelings. These feelings could be a desire to help, or a desire to quickly rid oneself of an unexpected problem. They might also include a desire to escape from something feared, to make some easy money, or to receive some sort of benefit (“…but you must act now!”). This same principle is used by the stereotypical used car salesmen: they talk fast, tell you all about how incredible this limited-time offer is, and warn you about how much you’ll have missed out on if you don’t buy something right this moment.
Phone calls about how your husband or child got into an accident or has been arrested are based on the fear you feel for your loved ones. And of course, they urgently need money to pay a ticket or to cover emergency medical care.
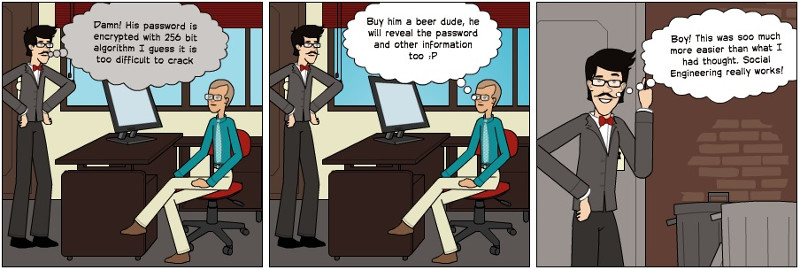
Why is social engineering so popular with cyber criminals? Most of all, it’s popular because it’s much easier to “hack” the average user, who is unprepared for a psychological attack, than it is to hack a computer system protected by all kinds of security measures.
The unfortunate conclusion: where social engineering works, information security is gravely at risk. Are there any means of avoiding it?
In our time, when so much of our business and personal lives is connected to the internet, it’s not enough to rely on technical tools to confront hackers. In corporate environments, separate network access rights and access to information which constitutes trade secrets as much as possible. Ideally, each employee has access to only the information needed for them to carry out their responsibilities.
Equally important is understanding the problem of social engineering and the significant risk it poses to personal and official data. Every user (especially users of company networks) must learn about the kinds of psychological attacks that could be used against them, and how to respond to them.
Subscribe To Our Newsletter
Join our mailing list to receive the latest news and updates from our team.

Subscribe To Our Newsletter
Join our mailing list to receive the latest news and updates from Protectimus blog.
You have successfully subscribed!