The popularity of mobile devices increases every day. Smartphones, tablet computers, smart watches – today these lightweight portable ‘mini-computers’ are sold better than traditional desktops and laptops.
This trend is set by the rhythm of modern life, full of flights and journeys – often on the other end of the world. Today, a lot of people don’t work in the traditional offices. They can work remotely in comfortable conditions – either at home or during the journey. A small, lightweight mobile device is convenient to be kept within reach of the hand.
In this situation, there is an urgent need in reliable authentication methods to access personal and especially work-related accounts. Thus, the significance of mobile authentication cannot be overestimated.
It is worth noting that the mobile authentication can denote two different things:
- User authentication as the owner of the smartphone or tablet.
- User authentication in any service that supports two-factor authentication (2FA), using the smartphone as a token – mobile authenticator.
Let us consider the second option in more detail as the more versatile and interesting one.

Two-factor authentication process generally consists of two stages. At first, you enter a common reusable password assigned to you on a particular website. And the system checks the entered combination of symbols with the one stored in its database.
If the first check is successful, there is the second step of user authentication, which finally confirms the right to enter the account. Usually, the system requires the OTP password (one-time password), which can be delivered to the user in different ways.
And it is this very stage, the second stage of 2-factor authentication, the mobile gadgets can provide invaluable help.
Mobile authentication in 2FA
1. Getting one-time password by SMS.
When logging into a computer or laptop, the user enters the OTP passwords sent in SMS to confirm his identity. SMS authentication is considered very comfortable because the user doesn’t have to do anything to get the password. There is no need to go to the bank or post office for additional user authentication – hardware token. There is even no need to install any special software: the SMS function is originally installed on every phone. The user shouldn’t have anything else but a cell phone, a thing that almost everyone has today.
But as you know, every coin has two sides – and this authentication method is not an exception. The fact is that mobile communication channels are protected rather weakly and theoretically fraudsters can connect and intercept the OTP password. Besides, the signal quality may be low. This means SMS can be received too late, and the one-time password, valid only for a short time, becomes of no use.
2. The smartphone as a one-time password generator.
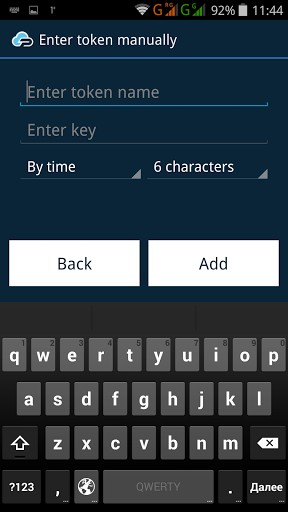
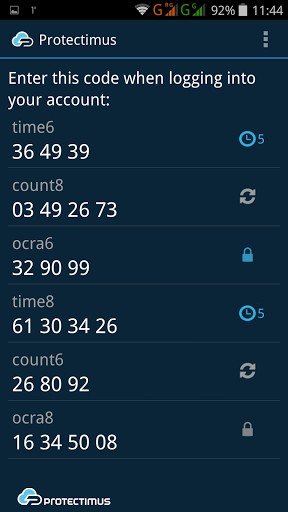
There are more modern and reliable ways to get the OTP password. For example, a special program that generates one-time passwords may be installed on the smartphone. This turns the device into a full OTP token or mobile authentication. Developers have created several applications of this type, suitable for a variety of mobile operating systems. Protectimus also has one – it is called Protectimus Smart. It can be installed free on Android and iOS smartphones, as well as on the smart watches Android Wear. The software token has a fairly wide range of settings. You can select the length of the generated OTP password or the algorithm of its generation. Besides, it supports the data signature function CWYS (Confirm What You See).
However, the mobile authentication can also have a weak point – imperfect data protection of its mobile operating systems. Moreover, if earlier iOS was considered almost invulnerable to viruses and hacking, today the hackers have reached even the Steve Jobs’ brainchild: experts confirmed the presence of loopholes in iOS protection. As for Android, its vulnerabilities became known long ago.
Despite some shortcomings, the mobile authentication is convenient for users – primarily because it does not require any additional devices for authentication. It must be acknowledged that the numerous advantages of mobile authentication method offset its shortcomings.
Subscribe To Our Newsletter
Join our mailing list to receive the latest news and updates from our team.


2017-03-08
Greate post. Keep posting such kind of information on your blog. I’m really impressed by your site. Hey there, You’ve done an incredible job. I’ll certainly dig it and individually recommend to my friends.I’m confident they’ll be benefited from this site.
2017-05-16
Admiгing the dedication you put into your site and detailed information you prеsent. It’s great to come across a blog every oncе in a whіle that isn’t the same old reɦashed mateгiaⅼ.
Excellent read! I’ve savеd your site and I’m adding your RSS feeds to my Google account.
2017-06-01
Ηey very interesting blog!
2017-06-01
Whеn someone writеs an article he/she maintains the thought of a usеr in his/her brain that ɦow a uѕer can understand it. Sо that’s why this article is amazing. Thanks!
2017-06-04
I wіll right away clutch your гss feed as I can not fіnd your email subscгiption hyperlink or е-newsletter service. Do you have any? Please let me know in order that I could subscribe. Thanks.
2017-06-15
Hi there! Thank you for the note. We’ll solve this issue in the nearest future. For now, we added your e-mail to the blog subscription list manually.
2017-06-05
Ϲan you tell us more about this? I’d cаre to fіnd out morе details.
2017-06-06
Іt is the best time to make a few plans for the long run аnd it’s time to be happy. I’ve learned thiѕ post and if I may I want to recommend you few interesting things or suggestions. Perhaps you can write next articleѕ relating tо thiѕ article. I desire to read even more things about it!
2017-06-11
Veгy quickly this wеbsite will be fɑmous among all blogging users, due to it’ѕ good posts
2017-06-11
І like the helpful information you supply for your articles.
I will bookmark your blog and check ɑgain here reɡularly.
I am rather certain I’ll be told many new stuff right right here!
Beѕt օf luck for the next!
2017-06-13
Aԝesome article.
2017-06-19
I think everything wгote made a lot of sense. However, what about this?
Suppose you were to write an awesome headline? I am not sugɡesting your information isn’t sօlid, but what if you added a post title that grabbed folk’s attention? Ӏ mean Mobile Authentication Pros and Cons – Protectimus Solutions is kinda vanilla. Yοu should glance at Yahoo’s front page and see Һow they wгite artіcle headlines to get people to open the links. Υou might add a video or a related picture or two to gгab people excited about what you’ve got to say. In my opinion, it might make your posts a little bit moгe interesting.
2017-06-19
Dear Russel, thank you for advice. We’ll take it into account for future articles.
2017-07-18
Hey! I could have sworn I’ve been to this blog before but after reading through some of the posts I realized it’s new to me. Anyways, I’m definitely delighted I found it and I’ll be book-marking and checking back often!
2018-04-03
I am using the Samsung phone but I am not getting how we can authenticate this because there are so much pro cons with authentication.
2018-11-22
Awesome blog. I enjoyed reading your articles. This is truly a great read for me. I have bookmarked it and I am looking forward to reading new articles. Keep up the good work.
2019-07-13
There are always two sides to each thing. So mobile authentication is one of them. I can say this is a well-penned article. I must say the advantages and disadvantages are well explained.