Did you know your Instagram two-factor authentication is ensured by a technology that has a backdoor as big as the one in the Titanic after it met the iceberg? Well, we will tell you more: the same faulty technology may still ensure the security of your Facebook and Twitter accounts! The last, but not the least important — you use the same technology to confirm most of your online purchases, so yeah — your banking account can be compromised as well. The name of that flawed technology is SMS authentication.
SMS based 2-factor authentication has few huge drawbacks, undermining the system functionality:
- SMS are stored and sent as plaintext on your smartphone and can be compromised with malware;
- SMS are transmitted over inadequately protected channels;
- Every mobile operator’s employee can change your phone number to another SIM card. Therefore, either by bribing a mobile operator’s employee with access to the SMS database or by using the technique known as “SIM porting”, the hackers can steal your Internet identity.
Meddling with OTPs opens up a wide field of manipulations — from stealing your Facebook, Twitter or Instagram account via the password reset procedure (which is exactly what happened when Katy Perry’s Twitter account was hacked) and up to stealing your banking accounts, as the banks still mostly rely on SMS to ensure the 2-factor authentication.
Fortunately, more and more services start moving to more secure two-factor authentication alternatives. And Instagram supports this good trend. On July 18th, 2018 an article on Techcrunch announced that Instagram started building non-SMS two-factor authentication.
Instagram is finally working on token-based two-factor authentication!! 🎉
Thank you Instagram! I have been waiting for this since 2016! We finally won’t have to rely our account’s security on SMS! 😍 pic.twitter.com/u0iIPTaZO2
— Jane Manchun Wong (@wongmjane) July 17, 2018
What’s wrong with SMS authentication?
1. SIM swap is real!
The hackers can contact the mobile operator’s technical support with a request to port your phone number to another SIM-card, and by completing the verification with the help of social engineering tactics, they will be receiving your SMS (including the ones with one-time passwords) from now on.
In fact, the issues with SIM porting has become so common and using SMS for two-factor authentication were proven to be so grave, that the US National Institute of Standards and Technology (NIST) has recommended dropping using SMS for OTP delivery back in 2016.
However, this call was not yet followed by the majority of the financial industry, healthcare, insurance and so on. Almost any business dealing with your Personally-Identifying Information (PIA) promotes using SMS two-factor authentication as an additional lever for ensuring the security or at least leaves this opportunity to their users.
| Read also: Dutch Scientists: SMS Verification Is Vulnerable
2. Your smartphone might be compromised with malware
SMSs are stored in plain text on your mobile device. Many models of smartphones are susceptible to specific Trojans like Perkele, Zitmo, Zeus or Citadel, which can be downloaded as a malware with some third-party apps and monitor the SMS messages with OTP codes. Thus said, as your smartphone is considered a safe haven device for the case when your PC or laptop are compromised, it is actually the smartphone that can provide the backdoor to your data.
3. Don’t rely on cellular network security
As the Global System for Mobile Communications (GSM) becomes an increasingly more attractive target for hackers, relying on its outdated security standards can be quite damaging for your finances and reputation. Due to the protocol specs, SMS are not encrypted during transmitting and can be easily scanned by malware in one of the mobile network provider’s hubs.
In addition, while SMSs are stored and processed in these Short Message Service Centers, they are susceptible to scans by malevolent or bribed employees. Specific malware like FlexiSpy can make copies of OTP messages and offload these logs to a remote server for further analysis and usage in scams and impersonation attacks.
| Read also: The Pros and Cons of Different Two-Factor Authentication Types and Methods
What 2FA Options Will Be Available in Instagram
If the situation is so dire, what other options for 2FA can Instagram users apply when non-SMS two-factor authentication for Instagram will be built? There are quite a few alternatives, from using third-party apps for authentication to leveraging specific hardware tokens.
Authentication apps
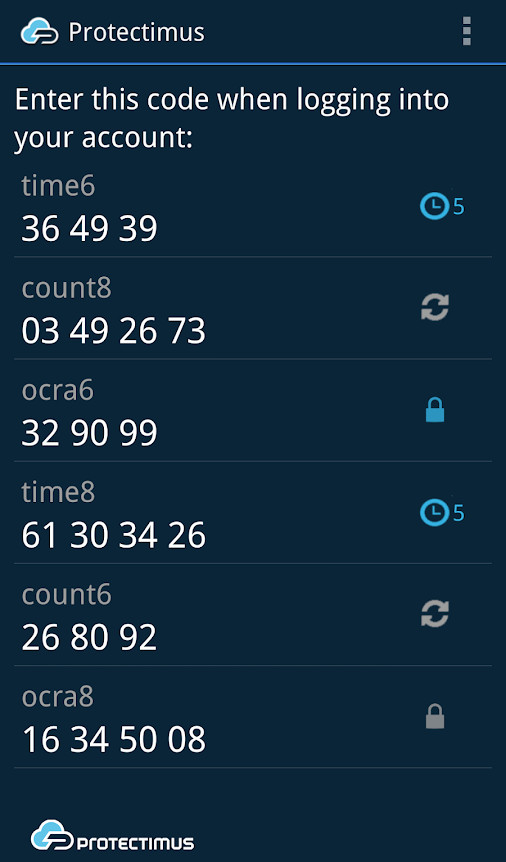
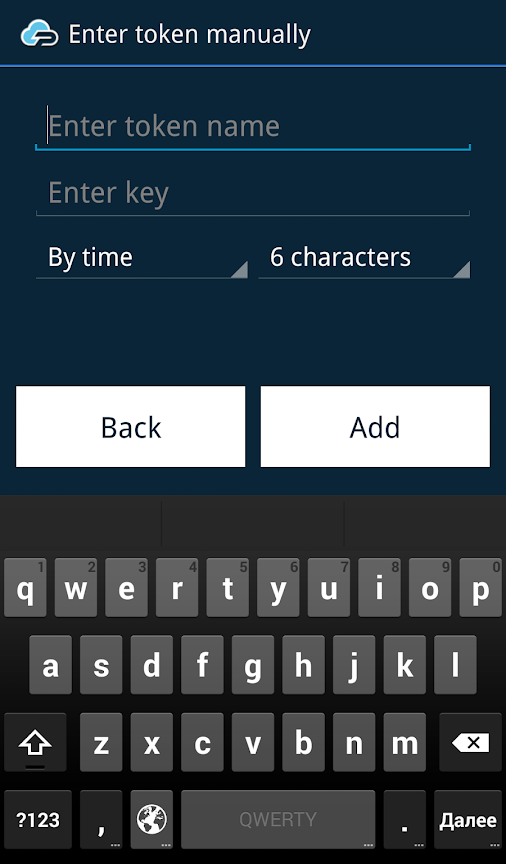
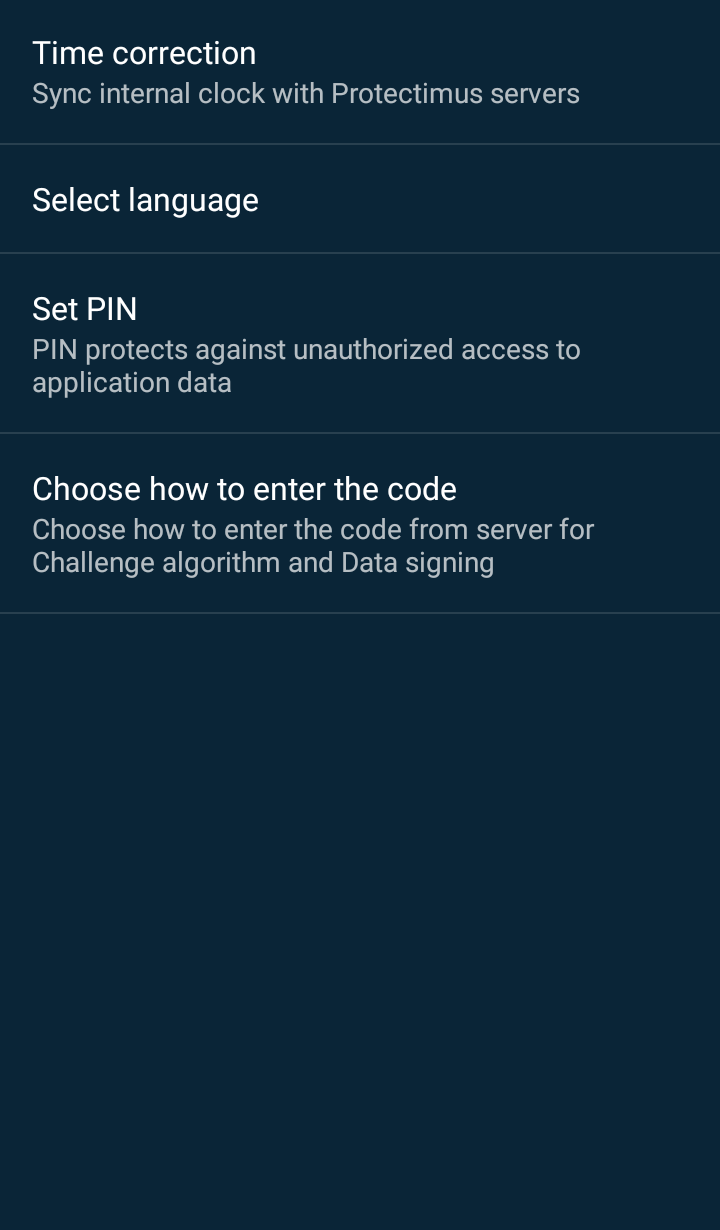
First of all, using third-party apps for 2FA, like Google Authenticator or Protectimus Smart, can be feasible.
To use the app for two-factor authentication in Instagram you’ll need to enroll the token first. To do this you’ll have to scan the QR code with the special secret key provided in your Instagram account. The app stores this code in the encrypted form and uses it to generate one-time passwords autonomously.
The app cannot be ported to another device, thus effectively removing the risk similar to SIM porting. And the OTP passwords are not delivered via any network, thus effectively removing the risk of OTP interception.
However, the malware infestation possibility remains, as well as some other issues:
- Should you reset your phone or delete the app if you didn’t save the secret code used to enroll the token, you are in a world of pain.
- If the battery is dead, no code can be generated, so no 2FA for you.
- The authentication app can still be hacked, undermining your security measures.
Thus said, while removing the risk of SIM porting, authentication apps still do not solve the problem entirely.
| Read also: Mobile Authentication Pros and Cons
Hardware tokens
The other solution is using the hardware OTP tokens Protectimus Slim NFC. These gadgets solve almost all the 2FA issues:
- Hardware OTP tokens cannot be infested with malware.
- This is a standalone device which generates one-time passwords without any internet or cellular connection, thus it cannot be intercepted.
- Of course, there is no any risk of SIM porting.
To use this token for two-factor authentication in Instagram you’ll need to program it with the secret key just like when using the 2FA application. There is an Android app Protectimus TOTP Burner to scan the QR code with the secret key and burn it to the OTP token via NFC. You can use this token with one website at a time, but if you decide to stop using Instagram, for example, the token can be reprogrammed and used with any other supported website.

All of the above makes Protectimus Slim Mini a worthy alternative to 2-factor authentication apps. However, its usage has certain limitations:
- It is a proprietary hardware that must be paid for.
- It works only for Android phones with NFC programming capabilities and cannot operate with iOS.
- The battery lifetime of the hardware tokens is limited and the battery is not replaceable, so you must change the token every 3-5 years.
However, these are not unsurpassable obstacles. If you indeed wish to ensure your Instagram security (as well as Facebook, Twitter, Dropbox, and banking accounts safety), and if buying a new token once every 5 years is not too much for you — using hardware tokens can be the best choice.
The only question is — do you really have to secure your Instagram login with two-factor authentication? Well, you definitely need to do this if you are Kim Kardashian or Donald J. Trump, or have any business connected Instagram activity.
| Read also: Hardware or Software Token – Which One to Choose?
Final thoughts on ensuring the security of your Instagram login
Thus said, while Instagram is actively working on implementing the non-SMS 2FA capabilities, you might make a step ahead and protect your device with either software or hardware tokens. This will ensure both Instagram login safety and protection for all of your digital assets. Should you make this step? The choice is up to you, of course, and if you have any questions — please let us know in the comments below!
Read more:
- How to Protect Your Privacy on Facebook
- Top 7 Tips How to Protect Yourself from Phishing Scams
- Social Engineering: What It Is and Why It Works
- What is Online Skimming and How to Avoid It
- Which messaging apps are trustworthy?
- Man In The Middle Attack Prevention And Detection
Subscribe To Our Newsletter
Join our mailing list to receive the latest news and updates from our team.


2019-04-24
I used 2FA with Duo for my Instagram account I accidentally logged out, was disconnected from Instagram on the Duo App and now cannot recover my account. I am in an endless loop of frustration. Instagram “help” hasn’t helped me and Duo can’t do anything.