To test the CWYS function and learn more about 2-factor authentication visit our demo page: Demo
Protectimus offers the following OTP tokens with the CWYS (Confirm What You See) function support:
 | Protectimus Ultra |
 | Protectimus Smart |
 | Protectimus SMS |
 | Protectimus Mail |
Let’s look at them in more detail.
Protectimus Ultra
It is a physical (hardware) token that has a number of advantages as compared to other hardware tokens, as described in more detail on our website.
From the point of view of the data signing function, it is somewhat inferior to other types of tokens because it is unable to visualize the data signed.
However, it still protects data from being modified or falsified during the span of time between creating and performing a transaction.
Protectimus Smart
It is a software token and the most popular token in the company’s product line.
Its advantage lies in the fact that the data signing function is available for any token generated in it. The data signed can be visualized, and there is additional protection against manipulating the transaction data.
Diagram 1 shows the process of the CWYS data signing.
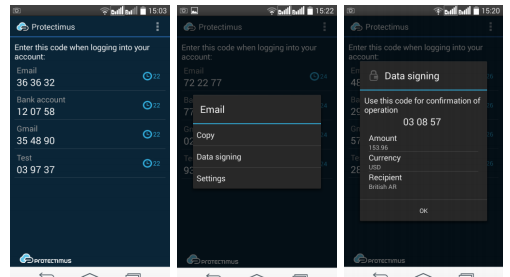
Diagram 1 – Data Signing in Protectimus Smart
As you can see in Diagram 1, a user needs only to go to the context menu and select the data signing function, scan the QR code, and receive information about the transaction being performed and the ОТР to confirm it.
This token’s undoubted commercial advantage is the fact that it is provided for free.
Protectimus SMS
It allows receiving the information on the transaction being performed, together with the OTP, via the user’s phone. The downside of this method is the disadvantages of using an SMS message to deliver authentication details.
This token’s advantages include simplicity of use and generation by the user.
Protectimus Mail
It allows receiving the information on the transaction being performed via email. Although this adds yet another verification channel, it should be noted that generally speaking this token does not provide full-scale two-factor authentication because email is usually also password protected.
As always, the final choice is up to you. Our recommendation is to use Protectimus Smart or Protectimus Ultra for the CWYS mechanism and secure protection of your system against auto-filling, injecting, and other types of manipulating the user data involved in performing transactions.
Subscribe To Our Newsletter
Join our mailing list to receive the latest news and updates from our team.

Subscribe To Our Newsletter
Join our mailing list to receive the latest news and updates from Protectimus blog.
You have successfully subscribed!