The RFID technology simplifies the process of cashless payments and is used by international payment systems MasterCard (PayPass) and Visa (PayWave). The convenience of such cards is that when making a purchase for an amount not exceeding a bank-specified limit (in the EU – 25 euros, in the U.S. – $15, in the U.K. – 20 pounds, in Russia – 1000 rubles), the owner doesn’t have to enter the PIN-code or leave a signature on the check.
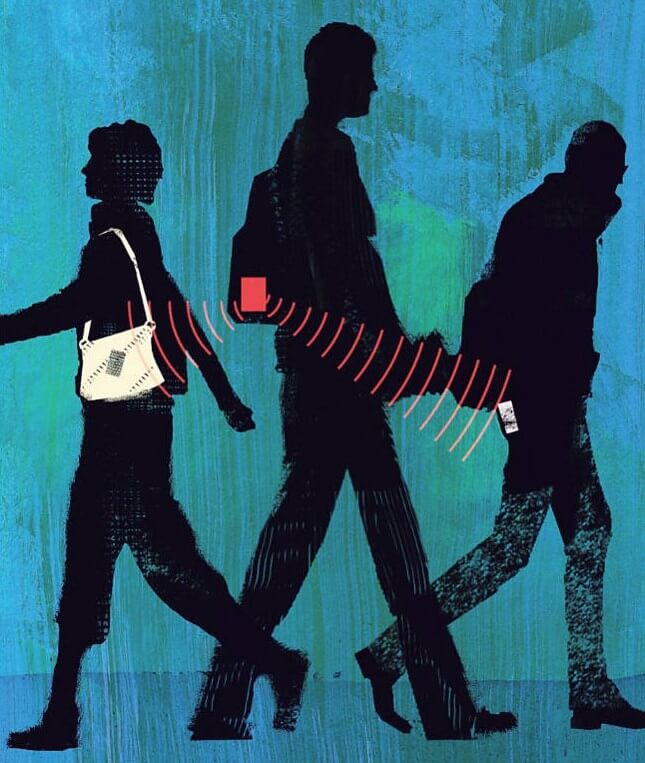
A crooks’ scenario is similar to that of car hijackers. Their task is to get closer, wait for the right moment and seize the necessary data promptly – whether it’s an intercepted signal of an electric lock or an RFID credit card fraud. To steal money from the bank cards remotely the crooks use improvised contactless readers, which work similar to a PoS-terminal – a legal RFID-reader, but they are much more functional.
To obtain the necessary information the hackers need to move this reader to the card at a distance of 5-20 centimeters. The thus-obtained data is either saved or transmitted to the counterfeit cards for future use.
Even if the card with an RFID-chip is PIN-protected, its number and expiration date are enough for illegal transactions or even creation of a counterfeit magnetic stripe of the card. Coming from the above, even if your wallet with credit cards is securely hidden from prying eyes and hands deep in a pocket or handbag, you can still ‘get robbed’ in a public transport, street crowd, or even at a cash register at a supermarket. Any owner of a card with a contactless payment technology can be attacked.
| Read also: The Most Common Ways of Credit Card Fraud
How to get protected against RFID credit card fraud?
There are not so many ways to protect yourself from the RFID credit card fraud:
- Data protection experts advise using special bags and wallets with insulation.
- It is also possible to complicate the task for the hacker having put a few credit cards in one place.
- Moreover, a few years ago Betabrand clothing manufacturer and anti-virus company Symantec cooperated to design jeans and blazers with pockets made using a special silver RFID-blocking material that prevents the scanner rays from passing through. Ready Jeans with a front and back left pockets being ‘under the Norton protection’ cost $168, and enjoy great popularity in the U.S. A Jacket Work-it at the cost of $198 is a little bit less popular than denims, but it is only because jeans are a more unique garment than the expensive blazer.
It’s sad that even if using all the above mentioned costly data protection methods and complying with all safety rules, we cannot fully protect ourselves from phishing, online skimming, social engineering, MITM attack, etc. Thus, as a two-factor authentication provider, we also advise to be always cautious, careful and turn on two-factor authentication for every online bank operation you do in advance.
Using 2FA for client authentication in a banking system or payment implies the need to confirm the legality of the operation with a one-time password (OTP) each time. Often one-time passwords are sent via e-mail, text messages, chatbots or push-messages, but it’s more secure to use hardware OTP tokens or a special smartphone 2-factor authentication application to generate one-time passwords.
| Read also: The Pros and Cons of Different Two-Factor Authentication Types and Methods
2FA is a reliable weapon in the fight against identity and money theft, because even having got your credit card data, a scammer cannot use it for fraudulent purposes during online payments. Besides, two-factor authentication can help you avoid becoming a victim of fraud working as an alarm. For example, a mobile phone message with a one-time password to confirm the operation you did not commit will immediately warn you about an attempt to get unauthorized access to your account and thus prevent a bank card fraud.
Read more:
- PayPal Two-Factor Authentication with Hardware Security Key
- How to Backup Google Authenticator or Transfer It to a New Phone
- 10 Windows Computer Safety Tips
- Phishing, Vishing, Smishing, Pharming – What Is the Difference
- How to Protect Facebook Account from Being Hacked
- Non-SMS Two-Factor Authentication for Instagram. Why Is It Good?
Subscribe To Our Newsletter
Join our mailing list to receive the latest news and updates from our team.

Subscribe To Our Newsletter
Join our mailing list to receive the latest news and updates from Protectimus blog.
You have successfully subscribed!