You thought all hackers are bad? It’s not so simple: in IT circles there has long been a distinction between “black hat” and “white hat” code crackers.
The first are easily understood: they are using their skills to deprive users and companies of money, and also prey on other valuable information for the purposes of identity theft.
But there are those who engage in hacking, not for gain, but with humanitarian and scientific motives. Such “good guys” are called white hat hackers. The main point of their work is to find vulnerable websites and services, and then notify the administrators of such resources. With the help of white hat hackers, administrators have eliminated a lot of bugs, and data protection in the network space becomes a more tractable problem.
Sometimes experts manage to find a “hole” even in those functions that were designed to protect against hacking. That’s exactly what happened with two-factor authentication. The Belgian white hat hacker A. Swinnen has found a clever way to earn extra cash by means of voice call-based 2FA. How can this be possible?
One of the main tasks of information security is to establish the legitimacy of the person requesting access to his or her account on a website, online bank, or payment system. To solve this problem, there exist numerous (often quite exotic) ways to authenticate users. The most reliable among them today is recognized as two-factor authentication using one-time passwords. The most common way of one-time passwords delivery is SMS authentication. But some companies use its modified version – voice calls to the number tied to the user’s account. This is the option used by A. Swinnen.
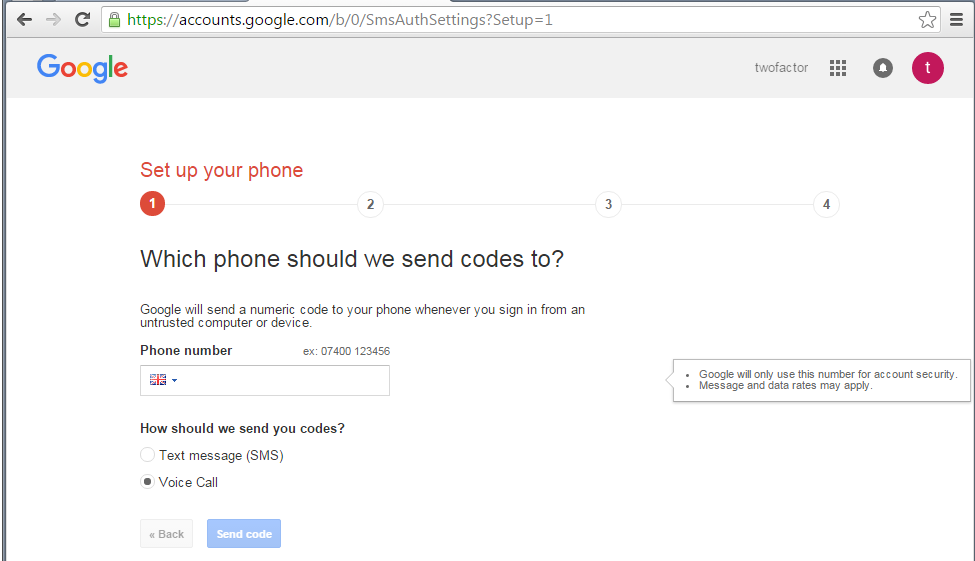
He set up experimental accounts in Instagram, Microsoft Office 365 and Google using phone numbers, calling and messaging which are not free. Unfortunately, the systems of these services could not determine that these were paid numbers. As a result, after each call, the companies were billed. The researcher found a way to make the robots used by Google, Microsoft and Instagram make calls to premium rate numbers as often as possible.
Swinnen calculated that for a year he would have been able to get somewhere between 2000 to 670 000 dollars, depending on the service targeted (the least promising was Instagram, and the most – Microsoft). The white hat hacker told developers about the problems he found at the end of 2015. Admittedly, all three companies have taken steps to eliminate the bugs that had been found in their two-factor authentication.
Such problems could be avoided altogether if companies used more robust and modern methods instead of SMS and phone calls. One of such solutions can be hardware or software OTP tokens, which generate one-time passwords offline. These devices do not use the Internet or telephone networks for the transmission of OTP passwords, which eliminates the possibility of fraud or one-time passwords interception.
Businesses relying on dual-factor authentication in their interaction with customers should remember that, though this is an excellent tool, it in itself is not a panacea against all threats. To make 2FA truly effective, its implementation should be well thought out. The developers should take into account all possible risks (which are often hidden in the most unexpected places). Don’t want fraudsters to find another loophole in your two-factor authentication system? Then contact the professionals.
Subscribe To Our Newsletter
Join our mailing list to receive the latest news and updates from our team.

Subscribe To Our Newsletter
Join our mailing list to receive the latest news and updates from Protectimus blog.
You have successfully subscribed!