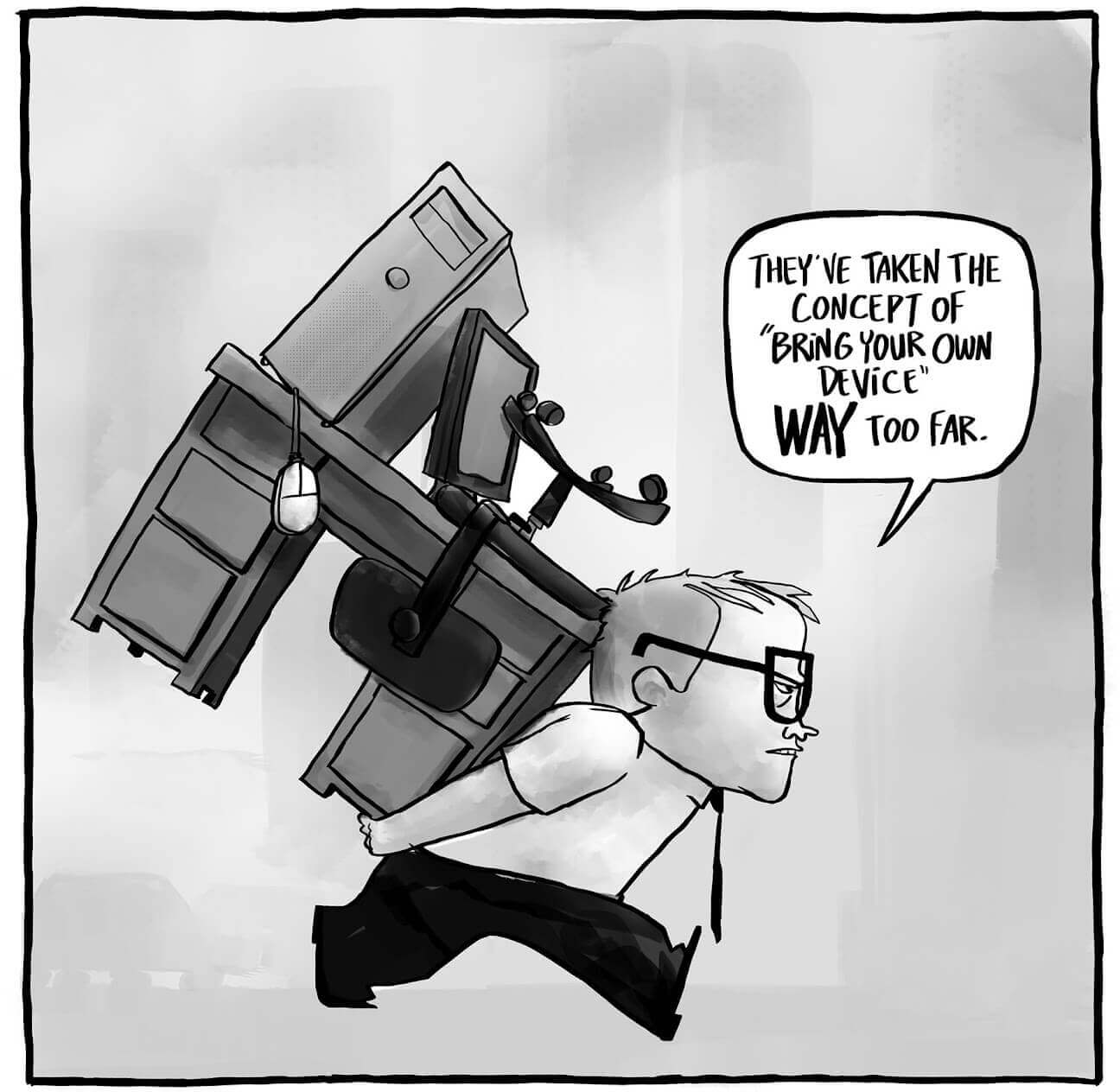
Up to now, not everyone knows what is BYOD (bring your own device). But anyone who uses a personal laptop or smartphone to gain access to corporate resources uses this technology even though may have no idea about it. This trend gradually penetrates even the “classic” offices, not to mention the companies whose employees work distantly!
The “bring your own device” concept emerged in the early 2000s. But an active transition from theory to practice started only in recent years. And now it is going on in front of our eyes. This is for two main reasons:
- We are witnessing an explosive growth of the number of personal mobile devices, which become more reliable, powerful, and affordable.
- The number of companies whose employees work remotely is also growing. Hiring freelancers doesn’t only save money for the office equipment but also helps to find and attract skilled professionals from all over the world.
Besides, we cannot forget about a psychological factor of the BYOD. A permission to use lovingly selected device significantly increases the employee’s loyalty to the company as they have a feeling of greater freedom and their motivation grows up. Many people unconsciously start spending a part of their personal time on the office tasks (for example, quickly responding to business correspondence, even when they are at home in free time). Thus, the work time expands – by the way, absolutely free of charge for the company.
It would seem that everything is fine: the staff is constantly in touch, always ready to discuss urgent business issues. And you can save money on the office equipment as well. But, like any coin, this one also has the other side: an uncontrolled use of BYOD technology can be critical to the company’s security (and thus revenue). It is well known that a “single” device is an easier target for cyber-criminals than a corporate network of trusted gadgets. And corporate information is for internal use only.
Is it possible to combine the confidentiality of corporate information and the use of personal laptops and smartphones? To do so, you must overcome two main mobile security challenges: vulnerability of mobile devices to viruses and nonchalance of their owners when it comes to information security. Both problems can be tackled if desired. You should only remember that BYOD security issues should be carefully designed and thought out in advance.
Basic BYOD security rules
- Antivirus and anti-spyware software approved by the IT-security department of the company and updated on a regular basis are compulsory on the employees’ devices.
- All BYOD devices should be connected to the corporate network via VPN.
- Mandatory encryption of data stored in the depository of the data center.
- Usage of a PIN-code to unlock a computer or smartphone and strong authentication to enter the accounts.
- Prohibition of use of jailbroken devices with unofficial operation systems. The users can resort to jailbreakers’ practices for different reasons: to improve the performance of their devices, get unlimited rights, install hacked or pirated applications. But there is no place for such “improvements” on a smartphone or tablet used to access the corporate network. And this should be clearly explained to employees.
- Creation of the technical possibilities to erase data remotely in case of a BYOD device loss or theft.
- Perhaps, the restriction of access to critical data from BYOD devices, and the use of geolocation to determine the level of access to data. For example, if an employee uses his own smartphone to enter confidential financial reports while at the workplace – the access is permitted. If the same device is used to authorize from a nearby cafe – the access is denied or restricted with only non-critical data being available.
- An automatic recording of unauthorized login attempts and other doubtful activities and immediate notification of the security system about such incidents.
- Engage the third-party experts in the process of finding gaps in the security systems of the corporate networks. As practice shows, the onlooker sees most of the game. Not without reason, many large companies, for example, Facebook, strongly encourage the network users to search for gaps in their security system and even pay finders rather large cash rewards.
- Regular check-ups of the gadgets involved in BYOD system for compliance with the information security requirements.
For the last few years, the BYOD concept has been lively discussed at various levels. It has both followers and critics, and they both put forward quite reasonable arguments to uphold their position. Who will win the dispute? Most likely, this will be the supporters of the BYOD technology. After all, today the concepts of working hours and workplace are getting increasingly blurred. The world annual increase in remote workers is 20-30%. Some companies are shifting to this working schedule in full, some partially. This vector of development ensures that the BYOD model will be inevitably used in all businesses more widely. The fact is that it must be done deliberately and carefully.
Picture by sysadminotaur.com
Subscribe To Our Newsletter
Join our mailing list to receive the latest news and updates from our team.

Subscribe To Our Newsletter
Join our mailing list to receive the latest news and updates from Protectimus blog.
You have successfully subscribed!